Technical Guides
Deep, expert-led technical guides on guest WiFi, analytics, captive portals, and venue technology.
296 guides
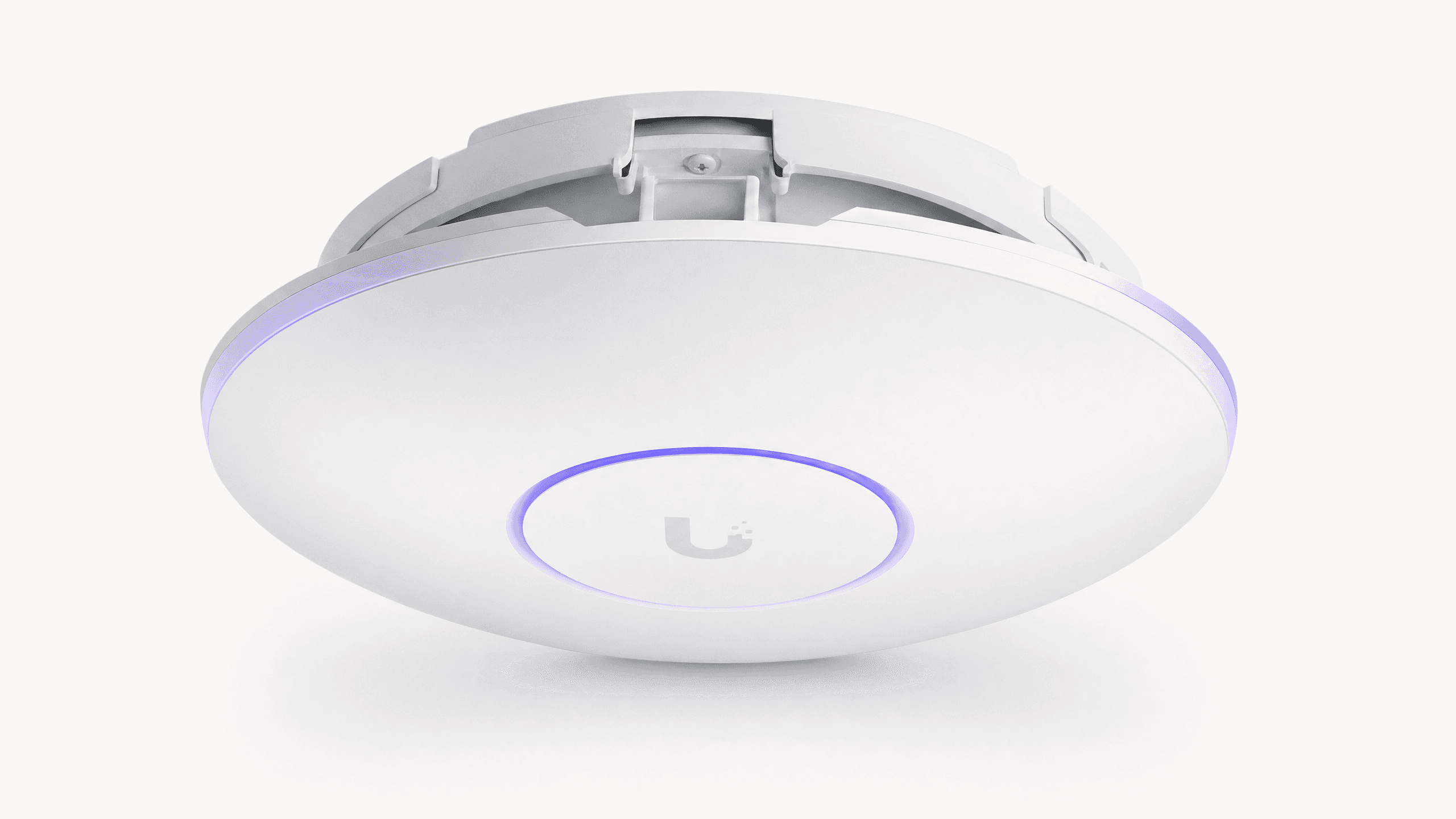
Indoor WiFi Positioning Systems: How They Work and How to Deploy Them
This comprehensive guide details the technical architecture, deployment strategies, and business value of WiFi-based indoor positioning systems. It provides network architects and IT directors with actionable guidance on AP placement, RF calibration, and overcoming MAC randomization to deliver precise spatial analytics.
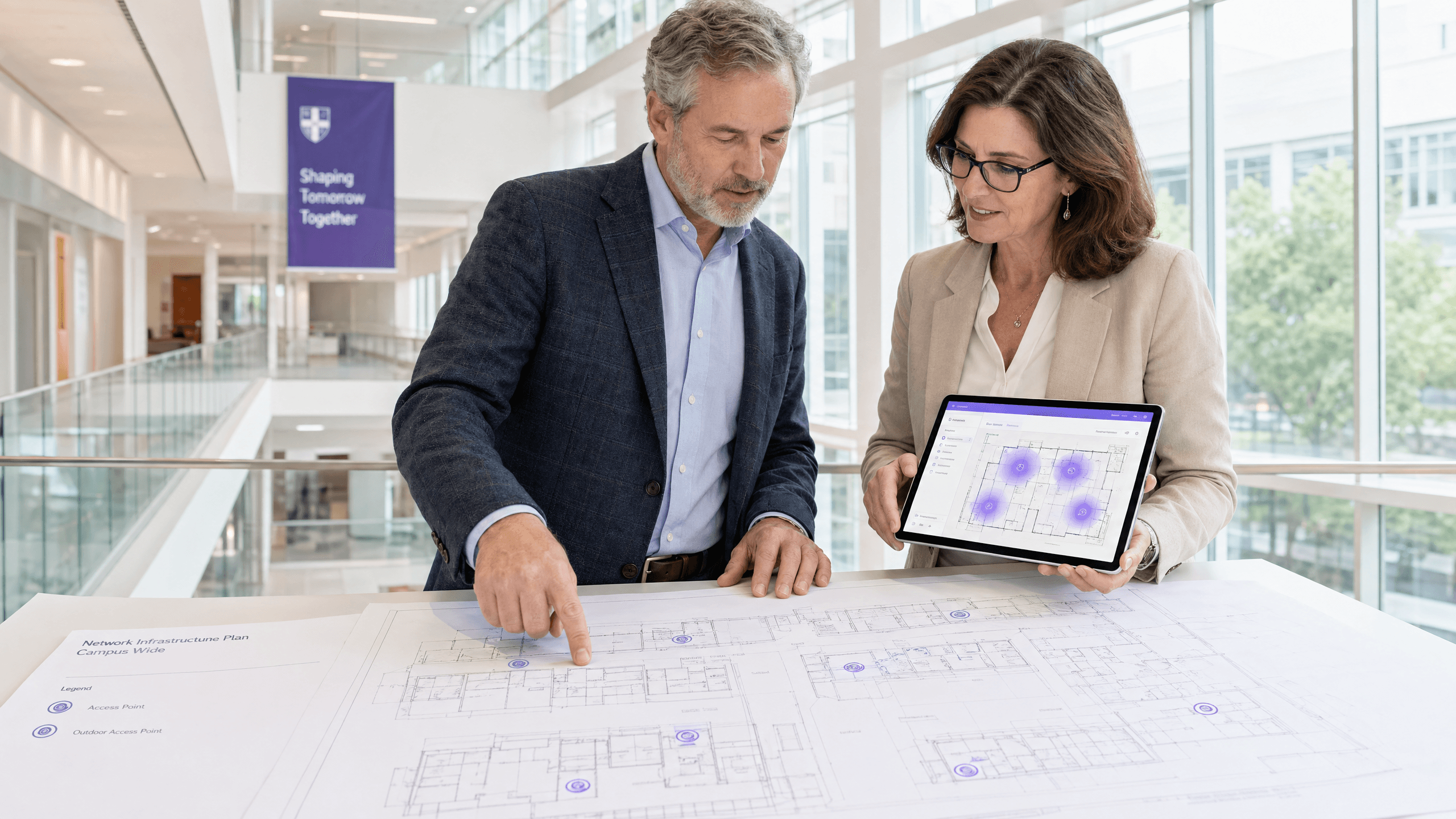
How to Build a Campus WiFi Network: A University IT Guide
This technical guide provides a comprehensive blueprint for designing and deploying high-density campus WiFi networks, covering everything from active site surveys and access point placement to controller architecture, seamless roaming, and secure guest onboarding. It is written for IT managers, network architects, and CTOs at universities and large venues who need actionable guidance to plan and execute a wireless deployment this quarter. The guide also maps Purple's Guest WiFi and analytics platform to real integration points within the deployment lifecycle.
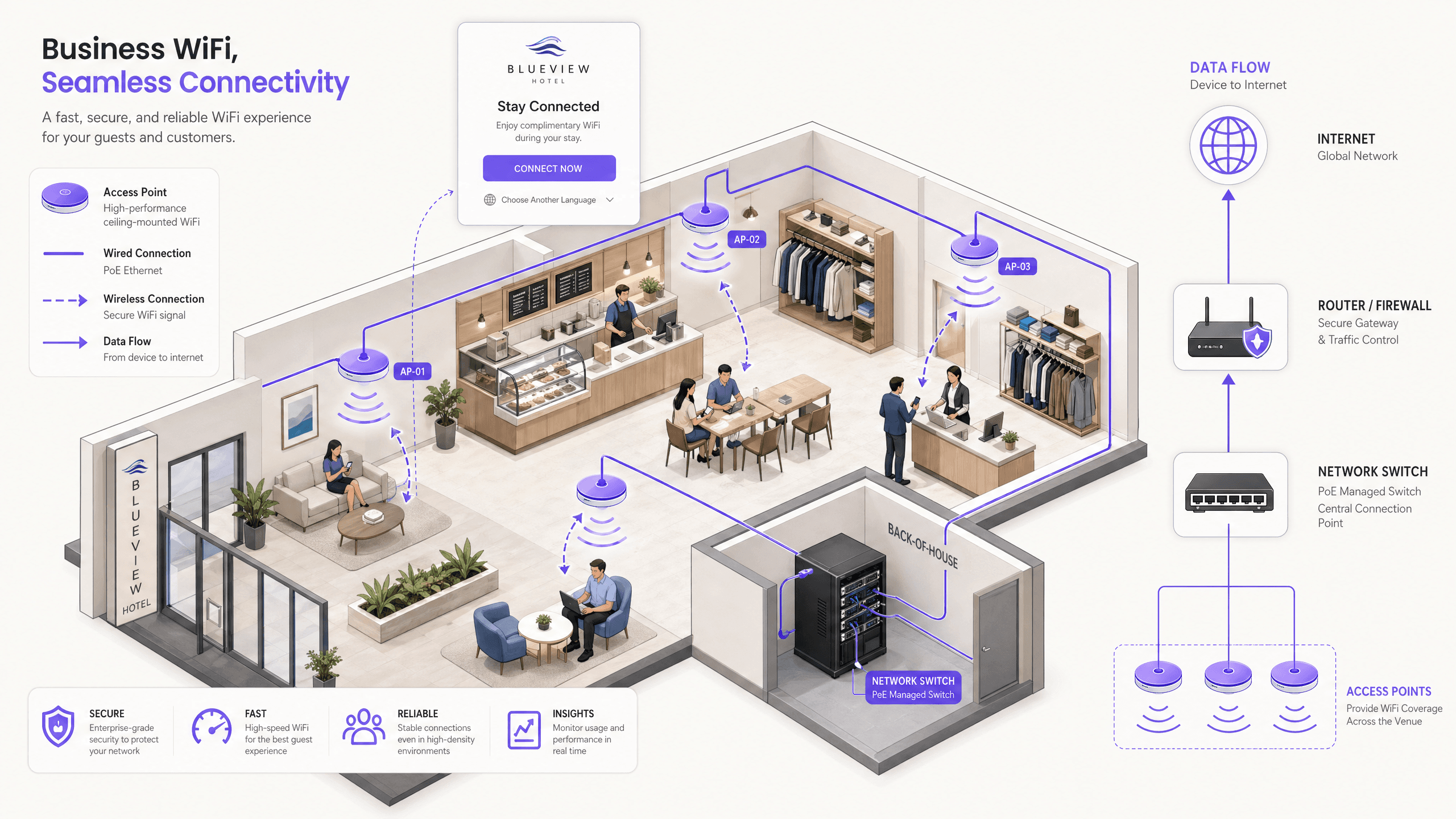
How to Set Up a WiFi Hotspot for Your Business
This authoritative guide provides IT leaders, network architects, and venue operations directors with a practical, vendor-neutral blueprint for deploying secure, compliant, and business-enhancing guest WiFi hotspots. It covers critical architecture decisions—from VLAN segmentation and captive portal configuration to GDPR compliance and traffic shaping—and demonstrates how to transform network infrastructure from a cost centre into a revenue-driving analytics platform using Purple's Guest WiFi and analytics capabilities.
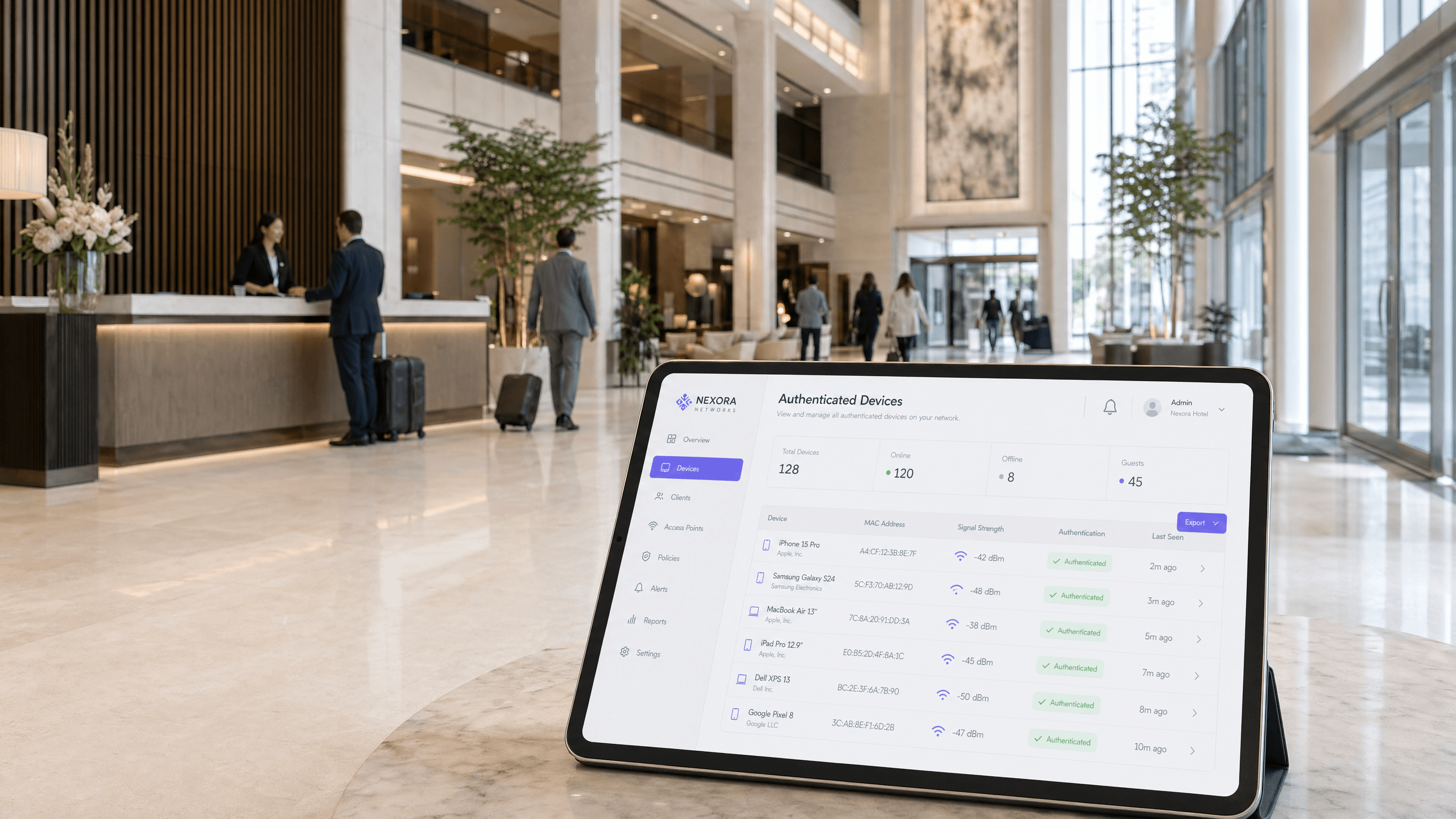
What Is MAC Address Authentication? When to Use It and When to Avoid It
This authoritative technical reference guide covers MAC address authentication in enterprise WiFi environments — how RADIUS-based MAC authentication works at Layer 2, its inherent security vulnerabilities (including MAC spoofing and the impact of OS-level MAC randomisation), and the precise operational contexts where it remains a valid tool for managing IoT and headless devices. It provides actionable deployment guidance for IT managers and network architects across hospitality, retail, healthcare, and public-sector venues, with real-world worked examples, decision frameworks, and integration context for Purple's guest WiFi and analytics platform.
RadSec: How RADIUS over TLS Improves WiFi Authentication Security
This authoritative technical reference explains how RadSec (RFC 6614) secures enterprise WiFi authentication by wrapping traditional RADIUS traffic in TLS encryption. Designed for IT managers and network architects, it covers architecture, deployment strategies, and practical steps to mitigate the risks of unencrypted UDP RADIUS traffic across corporate and guest networks.
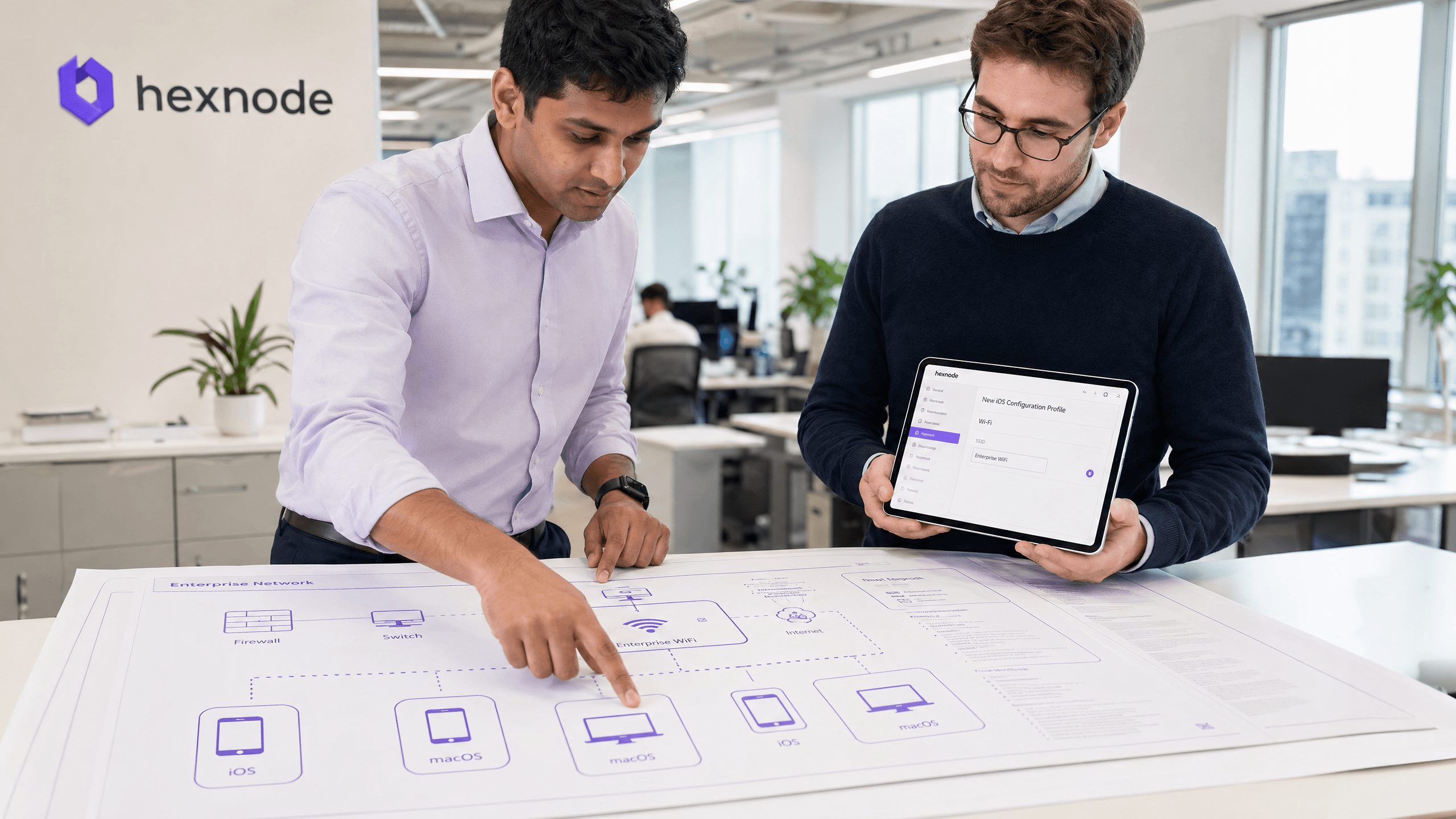
How to Set Up Enterprise WiFi on iOS and macOS with 802.1X
This authoritative guide provides senior IT leaders with actionable steps for deploying 802.1X enterprise WiFi on iOS and macOS devices. It covers certificate-based authentication (EAP-TLS), MDM configuration profiles, and architecture integration to secure corporate networks while supporting BYOD initiatives.
How to Set Up Enterprise WiFi on Android Devices with EAP-TLS
This technical reference guide provides senior IT leaders with a comprehensive blueprint for deploying 802.1X EAP-TLS authentication on Android devices. It covers the architectural mechanics, manual and MDM-driven implementation strategies, and troubleshooting methodologies necessary to secure enterprise wireless networks.
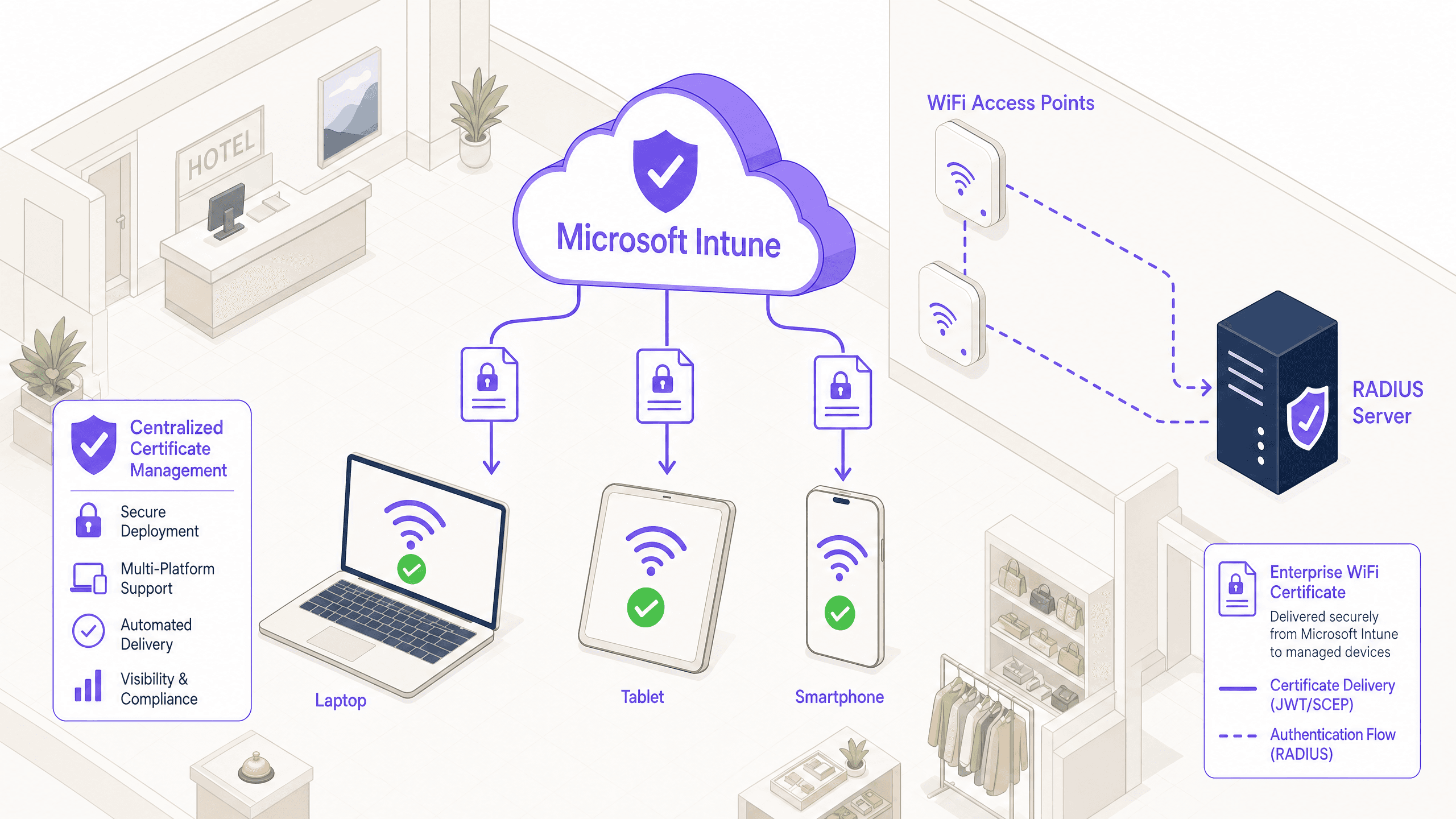
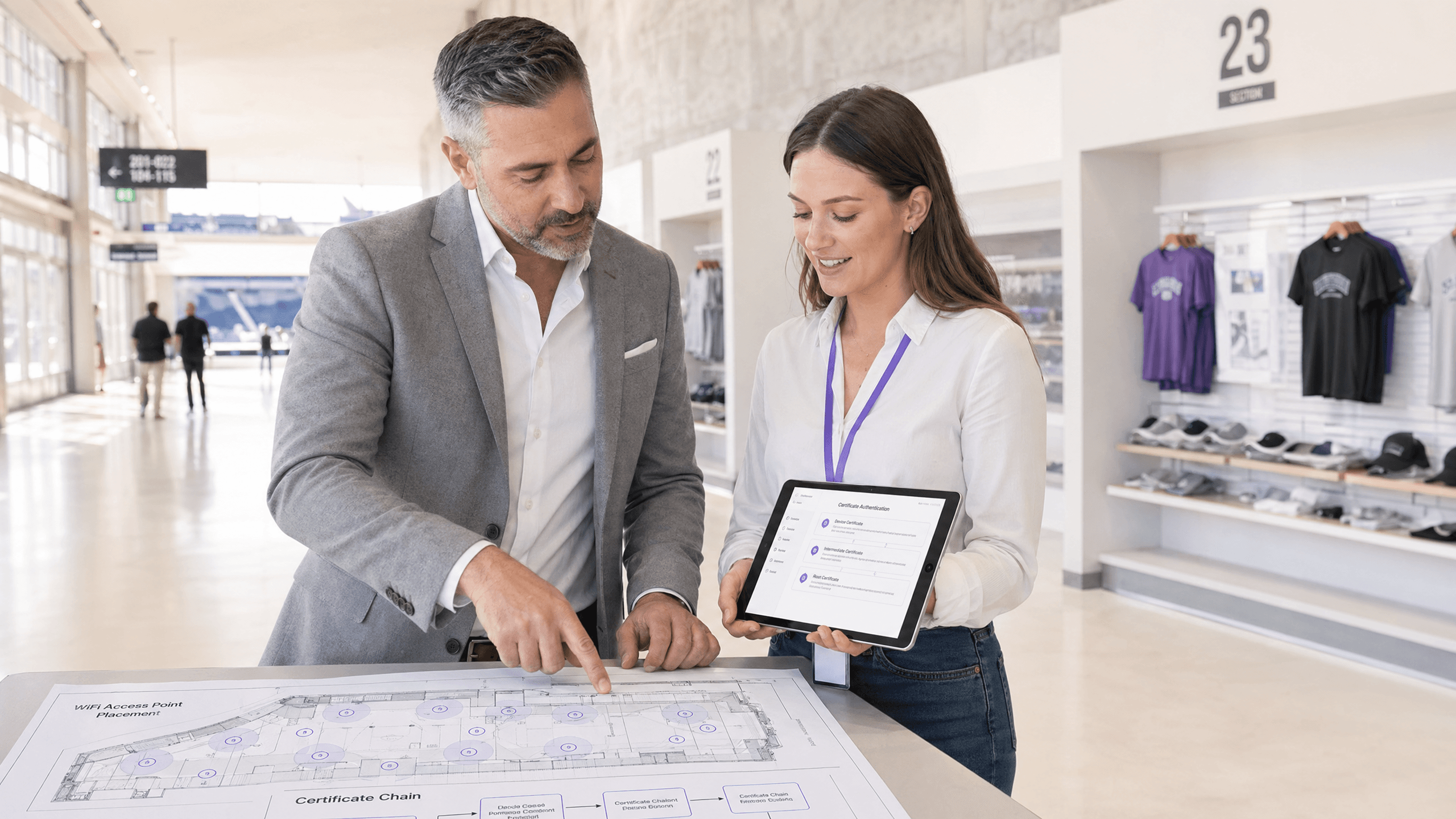
How to Utilise Microsoft Intune to Push WiFi Certificates to Devices
A comprehensive technical reference for IT leaders on deploying 802.1X WiFi certificates via Microsoft Intune. Covers SCEP vs PKCS architecture, implementation steps, compliance mapping, and real-world deployment scenarios for enterprise environments.
How to Set Up Azure Entra ID (Azure AD) for WiFi Authentication
This authoritative guide details the architecture, implementation steps, and business impact of integrating Azure Entra ID with 802.1X for enterprise WiFi authentication. It provides network architects and IT managers with practical deployment strategies, replacing legacy PSKs with zero-trust, certificate-based network access.

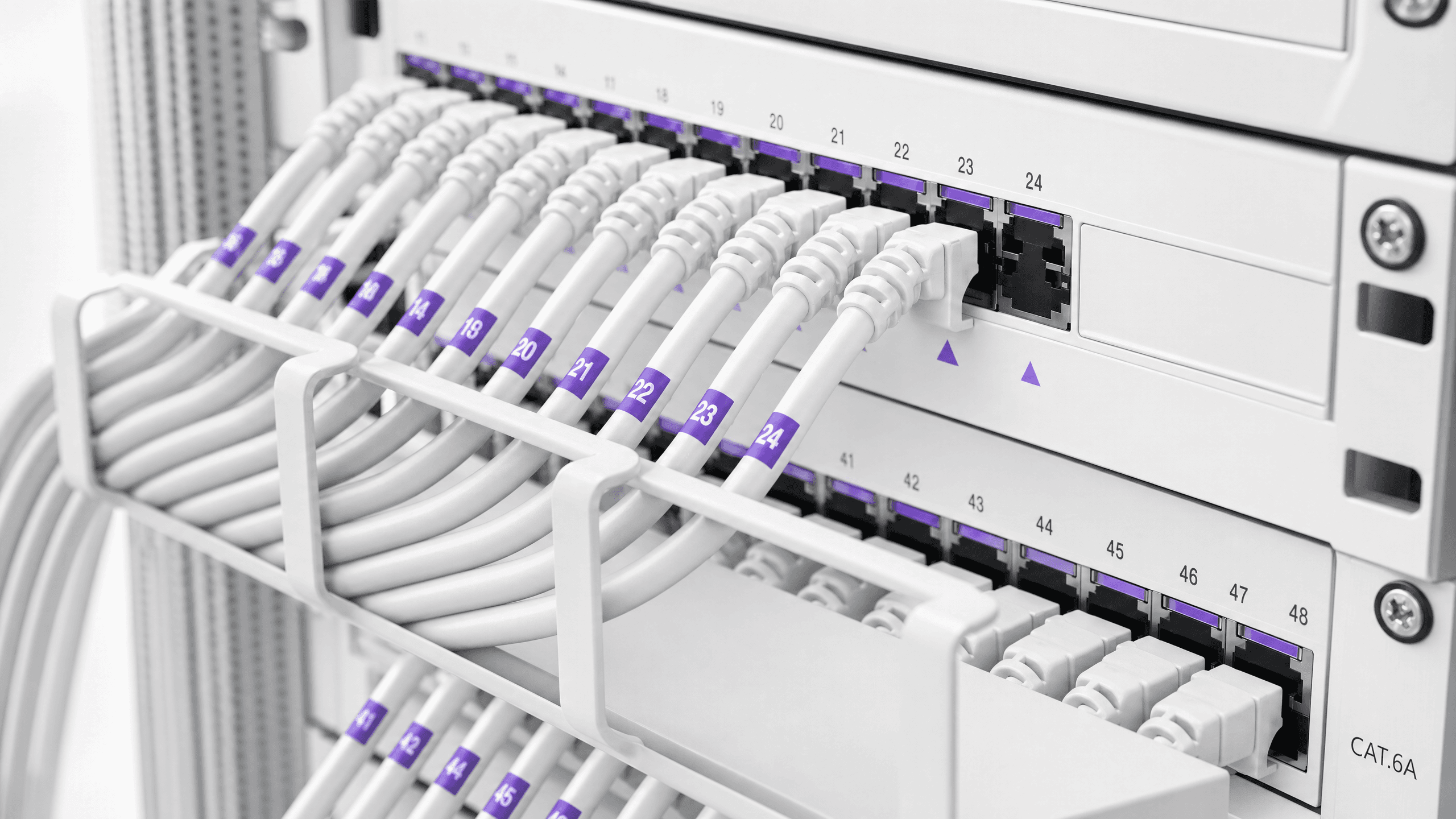
How to Configure WPA2-Enterprise on Common Access Point Platforms (Cisco, Aruba, Ubiquiti)
This technical reference guide provides senior IT professionals and network architects with a definitive, vendor-specific walkthrough for deploying WPA2-Enterprise on Cisco, Aruba, and Ubiquiti platforms. It details architecture, RADIUS integration, compliance requirements, and real-world deployment scenarios across enterprise and venue environments.
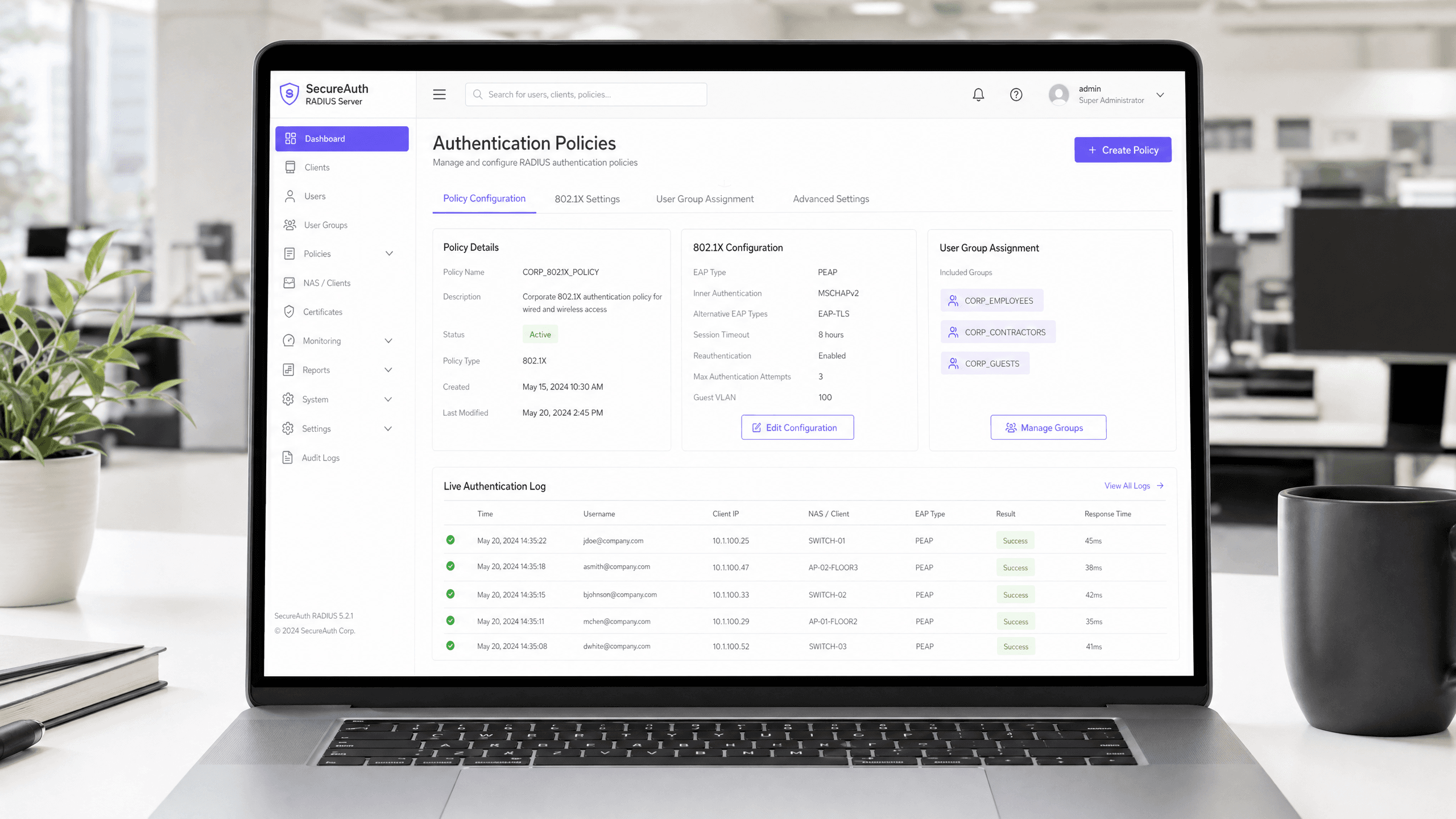
How to Set Up a RADIUS Server for WiFi Authentication
This authoritative guide provides IT leaders and network architects with a comprehensive blueprint for deploying a RADIUS server for enterprise WiFi authentication. It covers the architectural trade-offs between on-premise and cloud-hosted deployments, EAP method selection, Active Directory integration, and dynamic VLAN assignment. Venue operators and IT teams will find actionable implementation steps, real-world case studies, and risk mitigation strategies to move from an insecure PSK environment to a robust 802.1X infrastructure this quarter.
How to Configure 802.1X WiFi Authentication: A Step-by-Step Guide
This technical guide provides a step-by-step walkthrough for configuring 802.1X enterprise WiFi authentication. It covers RADIUS server setup, certificate deployment, and practical deployment strategies for IT leaders across high-footfall venues.
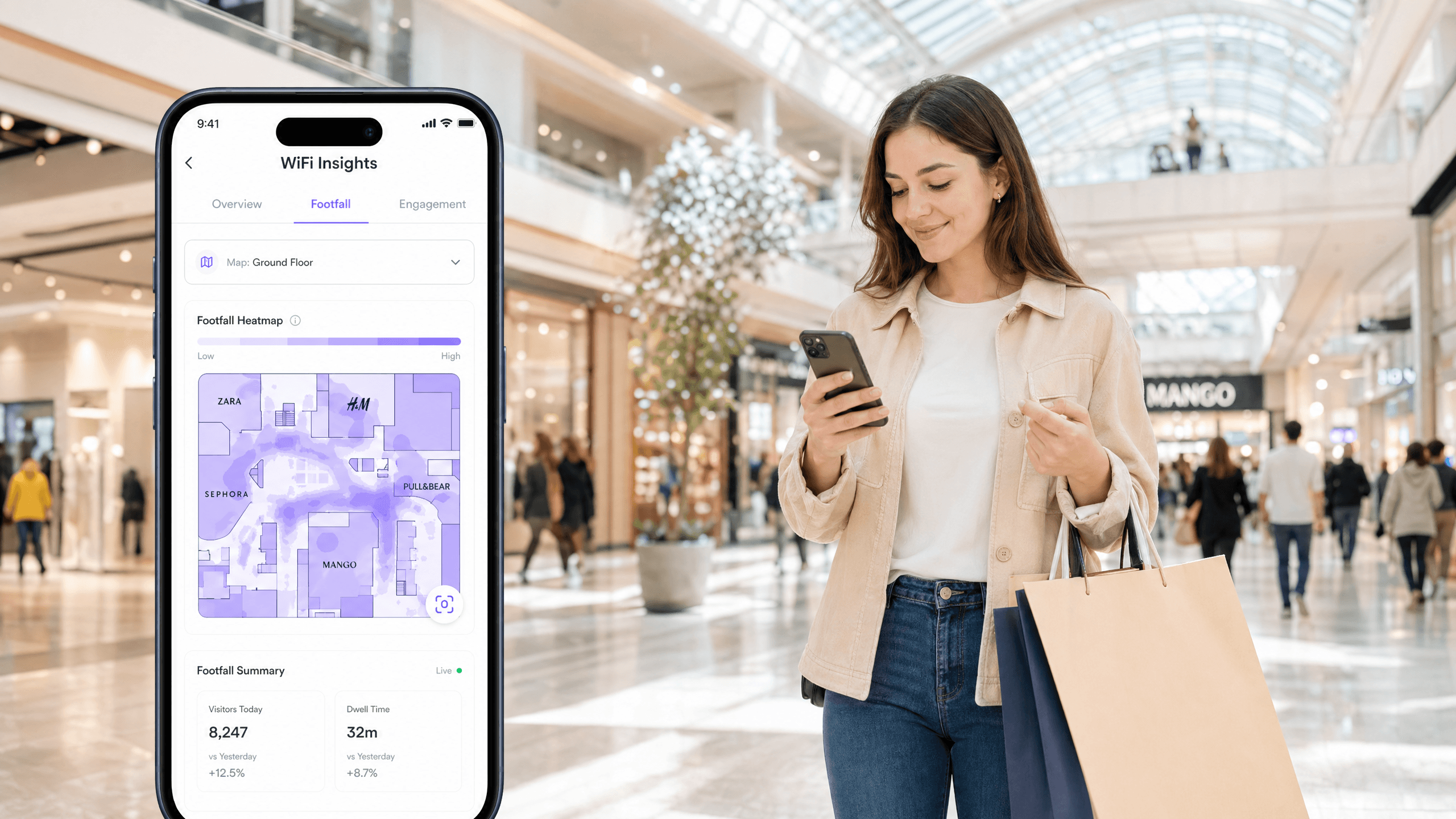
How Shopping Centres Use WiFi Analytics to Attract and Retain Retailers
This authoritative technical reference guide explains how shopping centre IT teams and property managers deploy WiFi analytics to capture footfall data, measure dwell time by zone, and build the empirical evidence base needed to negotiate leases, retain premium retailers, and attract new tenants. It covers the full technical stack from AP deployment and MAC-layer data capture through to GDPR-compliant analytics dashboards, with concrete worked examples and decision frameworks for IT practitioners ready to implement this quarter.
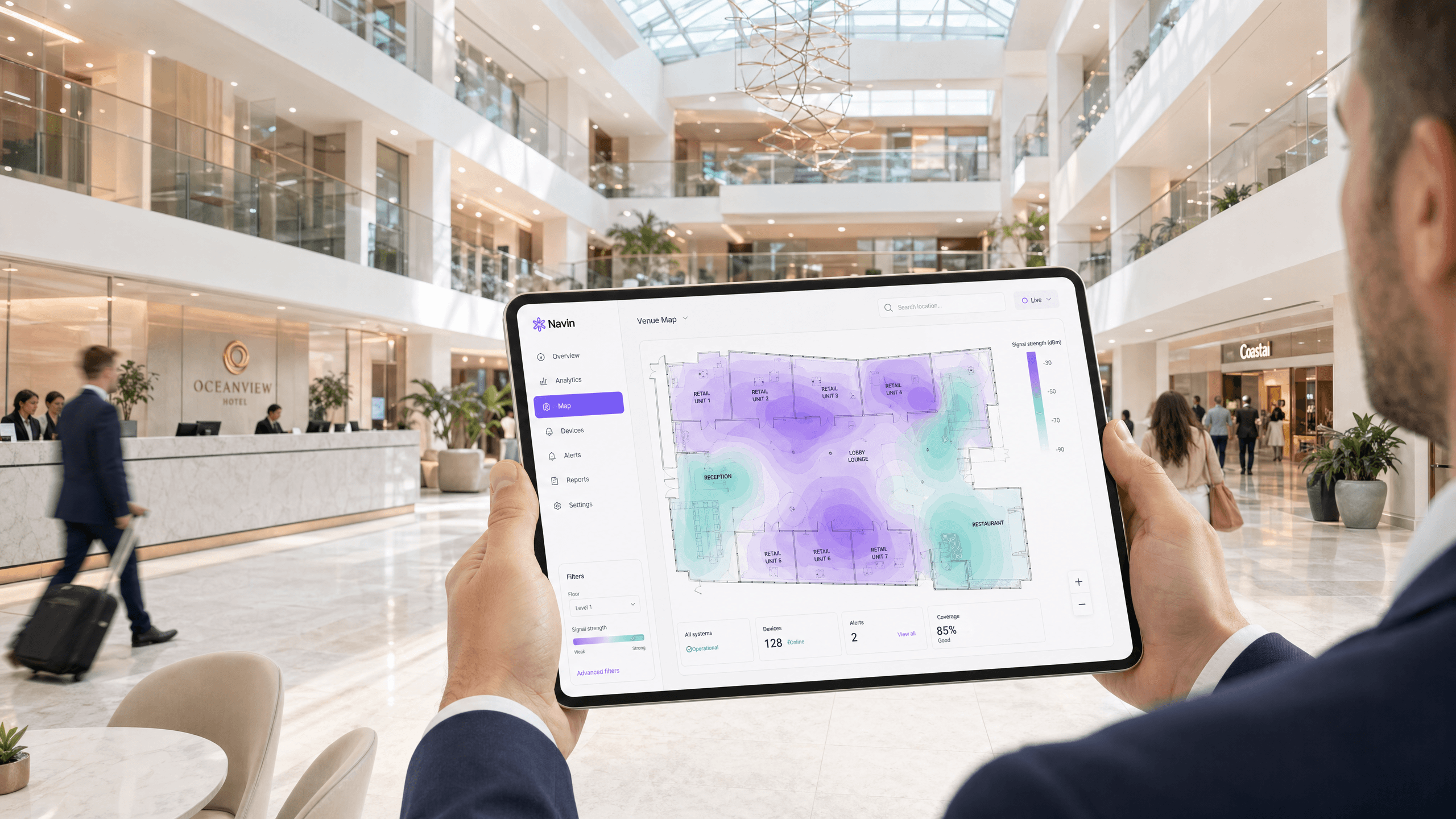
Shopping Centre WiFi: A Property Manager's Guide
This guide provides a comprehensive technical and commercial blueprint for deploying estate-wide WiFi across a shopping centre. It covers three-tier network architecture, high-density RF design, GDPR-compliant data capture, and retail media monetisation strategies. Property managers, IT teams, and CTOs will find actionable deployment guidance alongside a clear ROI framework for transforming guest connectivity into a first-party data asset.
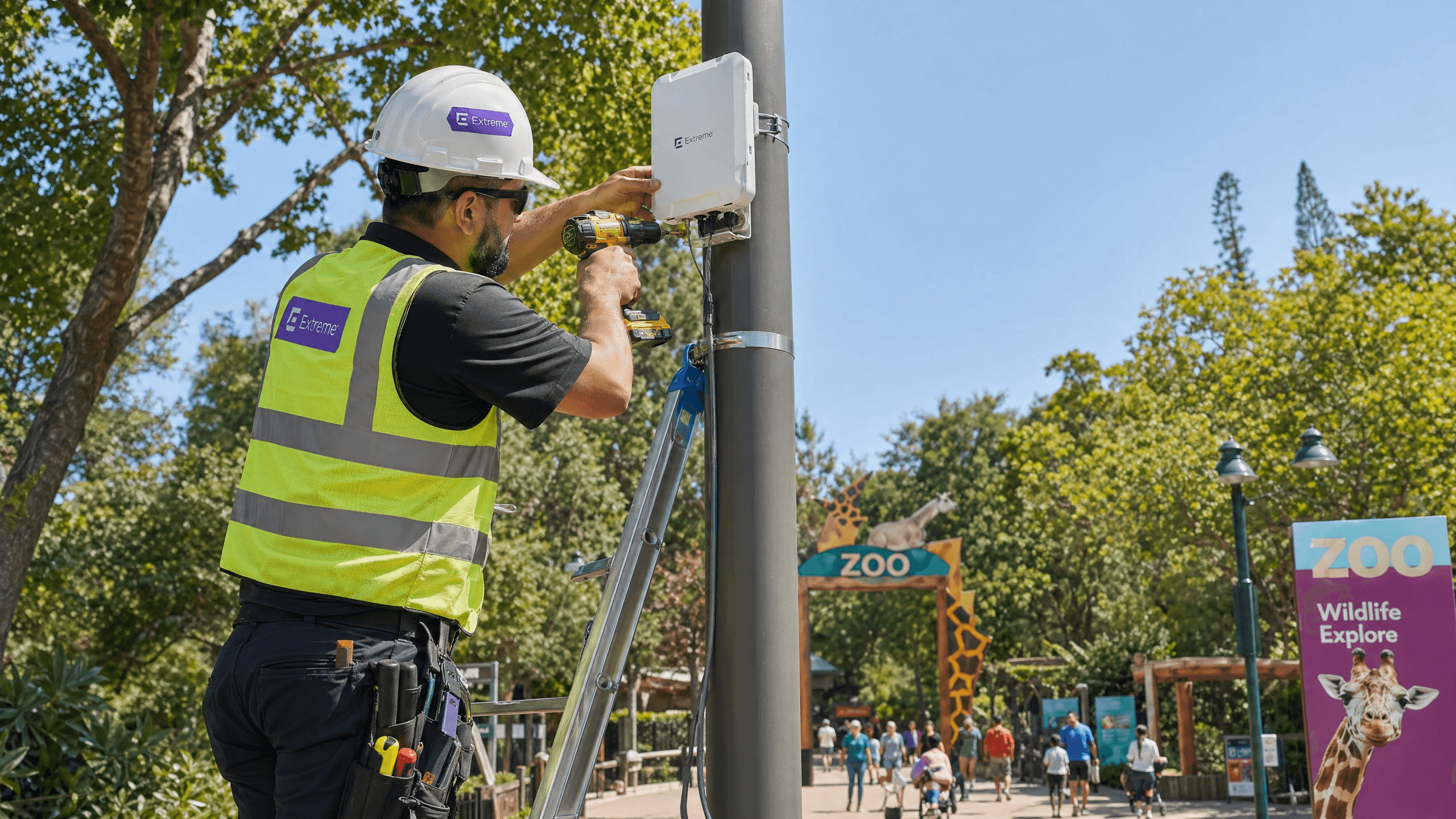
Zoo and Theme Park WiFi: High-Footfall Venue Connectivity Guide
This guide provides IT leaders and network architects with a comprehensive framework for deploying high-performance WiFi across zoos and theme parks. It covers outdoor RF planning, captive portal deployment, family-safe content filtering, and strategies for turning connectivity into actionable operational analytics.

eduroam and 802.1X: Secure WiFi Authentication for Higher Education
This authoritative technical reference guide explains the architecture, deployment, and security of eduroam and 802.1X authentication. Designed for IT managers and network architects, it covers practical implementation steps, EAP method selection, and how venue operators can securely support academic roaming.
Museum and Gallery WiFi: Creating a Connected Visitor Experience
This guide provides a comprehensive technical blueprint for deploying high-density WiFi in museums and galleries. It covers network architecture, visitor engagement strategies, and how to leverage WiFi analytics to drive ROI and operational efficiency.

Event WiFi: Planning and Deploying Temporary Wireless Networks
This guide provides IT managers, network architects, and venue operations directors with a complete technical reference for planning and deploying temporary WiFi networks at events of any scale. It covers capacity planning, hardware selection, VLAN architecture, captive portal integration, GDPR compliance, and post-event analytics — with concrete case studies from hospitality and large-scale conference environments. For event producers and AV companies, it maps the full lifecycle of an event WiFi engagement from initial site survey through to teardown and reporting.
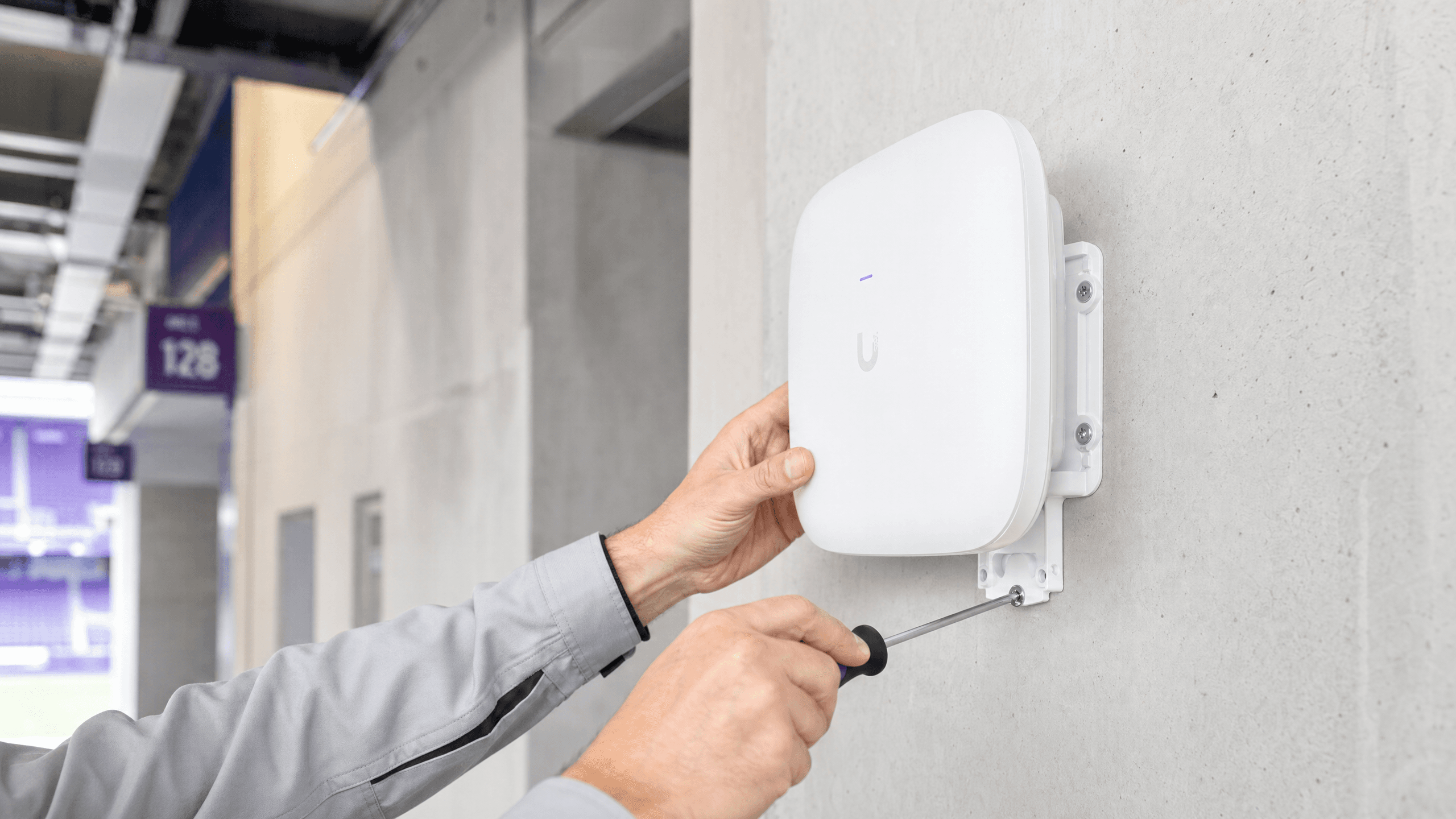
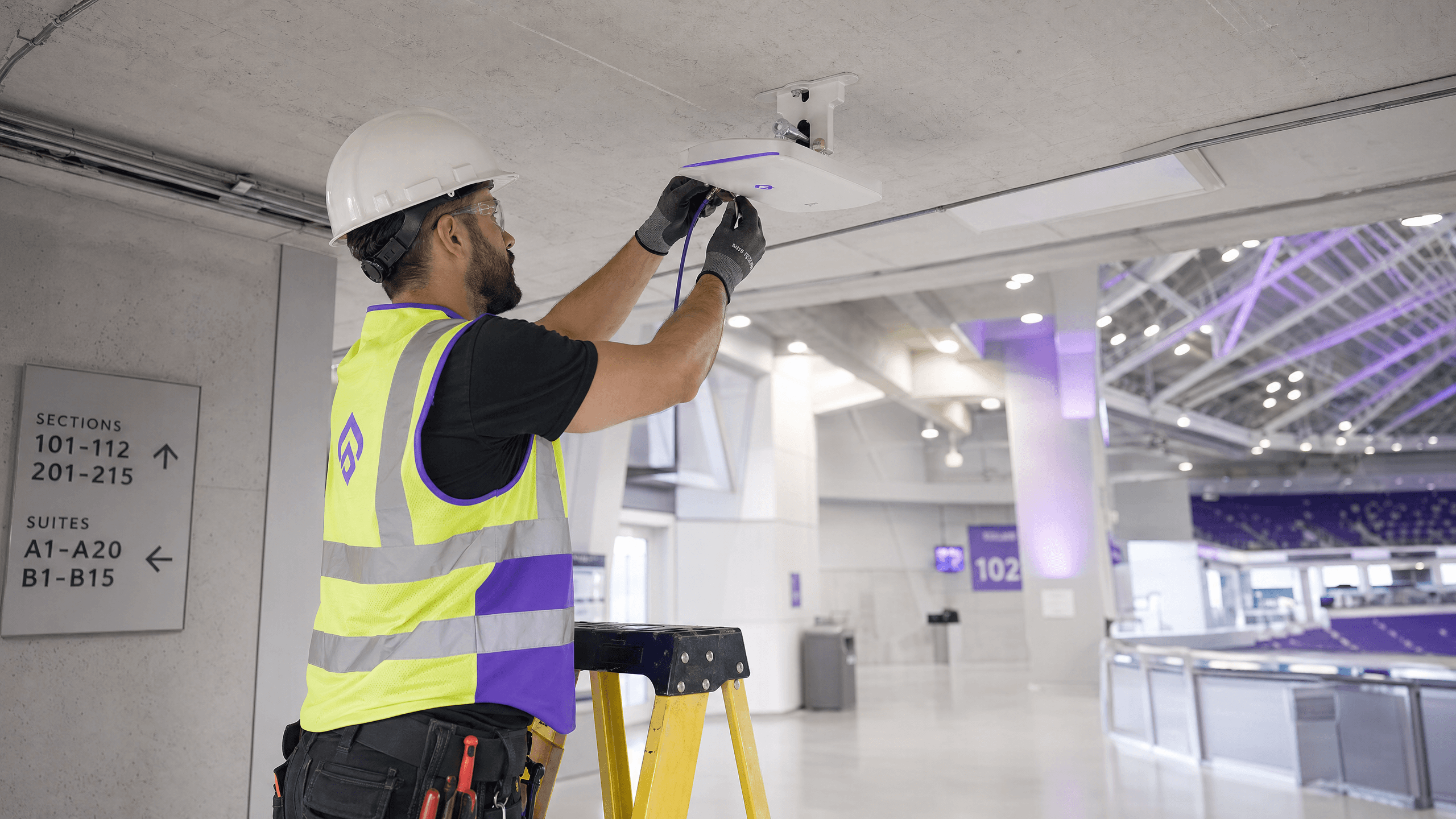
Stadium WiFi: How to Deliver Connectivity at Scale for Fans
This authoritative technical reference guide provides actionable guidance for IT managers, network architects, and venue operations directors on designing, deploying, and monetising high-density stadium WiFi networks. It covers RF architecture for extreme device density, secure authentication at scale, network segmentation, and risk mitigation — alongside practical case studies and a clear framework for measuring ROI. Venues that deploy correctly can transform their WiFi infrastructure from a cost centre into a strategic platform for fan engagement, retail media, and operational intelligence.
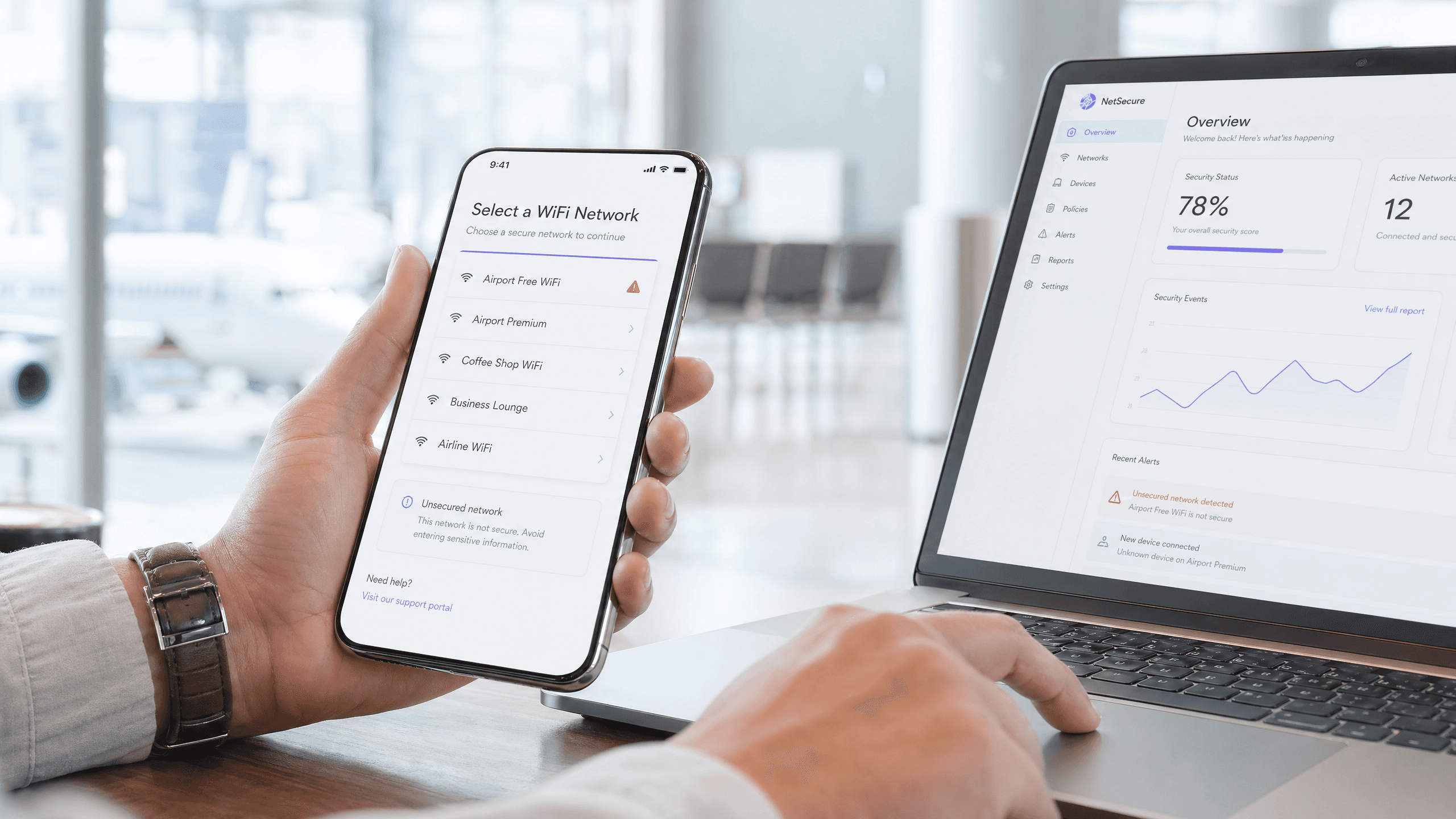
Airport WiFi Security: How to Protect Passengers on Public Networks
This technical reference guide details the specific threat landscape of airport WiFi, covering Evil Twin access points, rogue hardware, and Man-in-the-Middle attacks. It provides IT managers, network architects, and venue operations directors with actionable architectural strategies — including WPA3 implementation, VLAN segmentation, WIPS deployment, and GDPR-compliant captive portal design — to protect passengers and enterprise infrastructure at scale. Purple's guest WiFi and analytics platform is mapped concretely to each problem domain throughout.
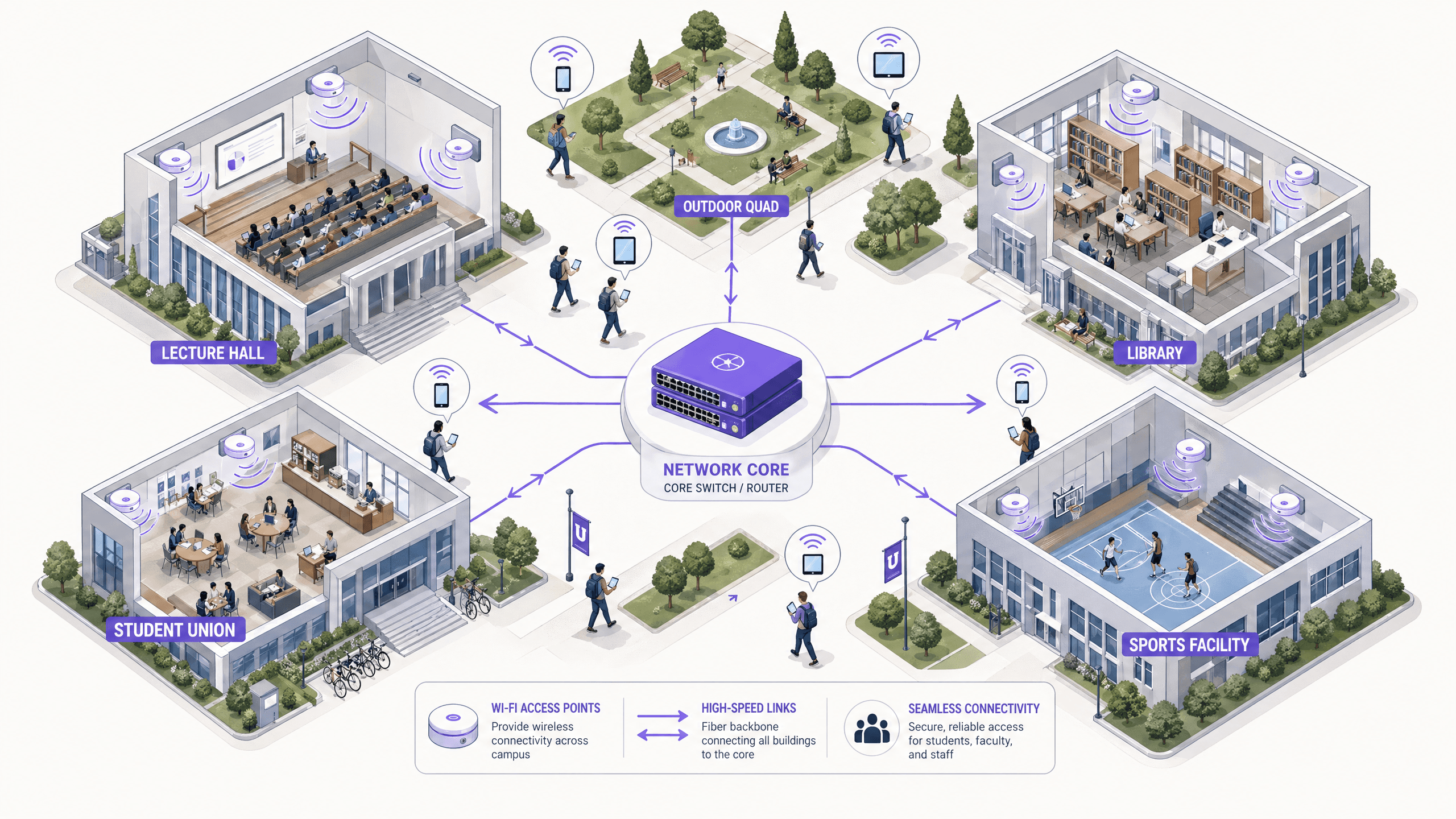
University WiFi: How to Build a Campus-Wide Wireless Network
This comprehensive guide provides senior IT professionals with actionable strategies for designing, deploying, and managing a robust campus-wide wireless network. It covers hierarchical network architecture, security standards (IEEE 802.1X, WPA3, GDPR), and how to utilise analytics to drive ROI in higher education environments. Whether you are upgrading legacy infrastructure or building from scratch, this guide maps every decision point from site survey to ongoing optimisation.
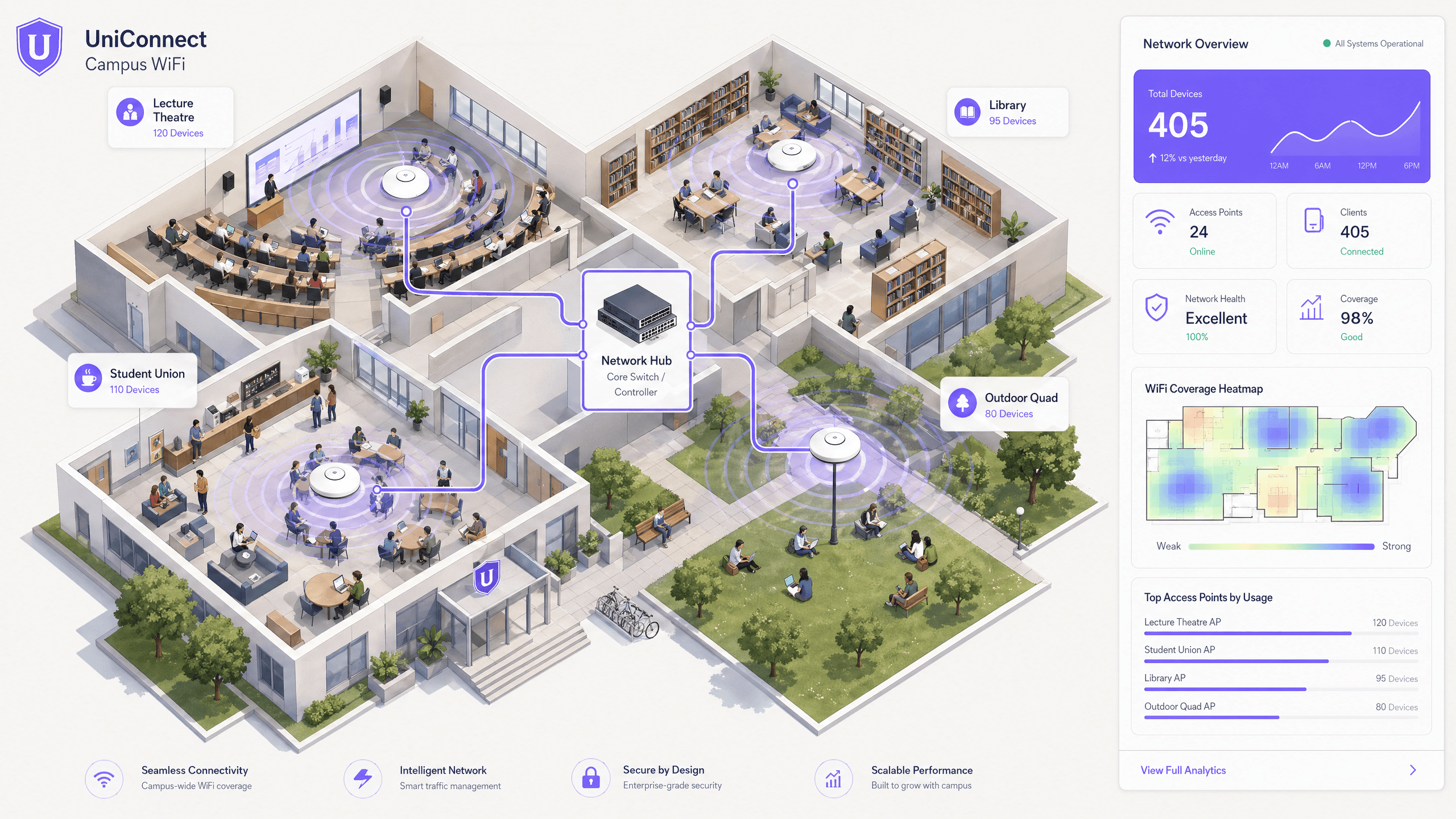
Student WiFi: What Universities Need to Get Right
This authoritative guide details the critical architecture, security protocols, and analytics required to deliver high-performance student WiFi at scale. It provides IT leaders with actionable strategies for managing BYOD density, implementing robust authentication, and leveraging network intelligence for estate management.
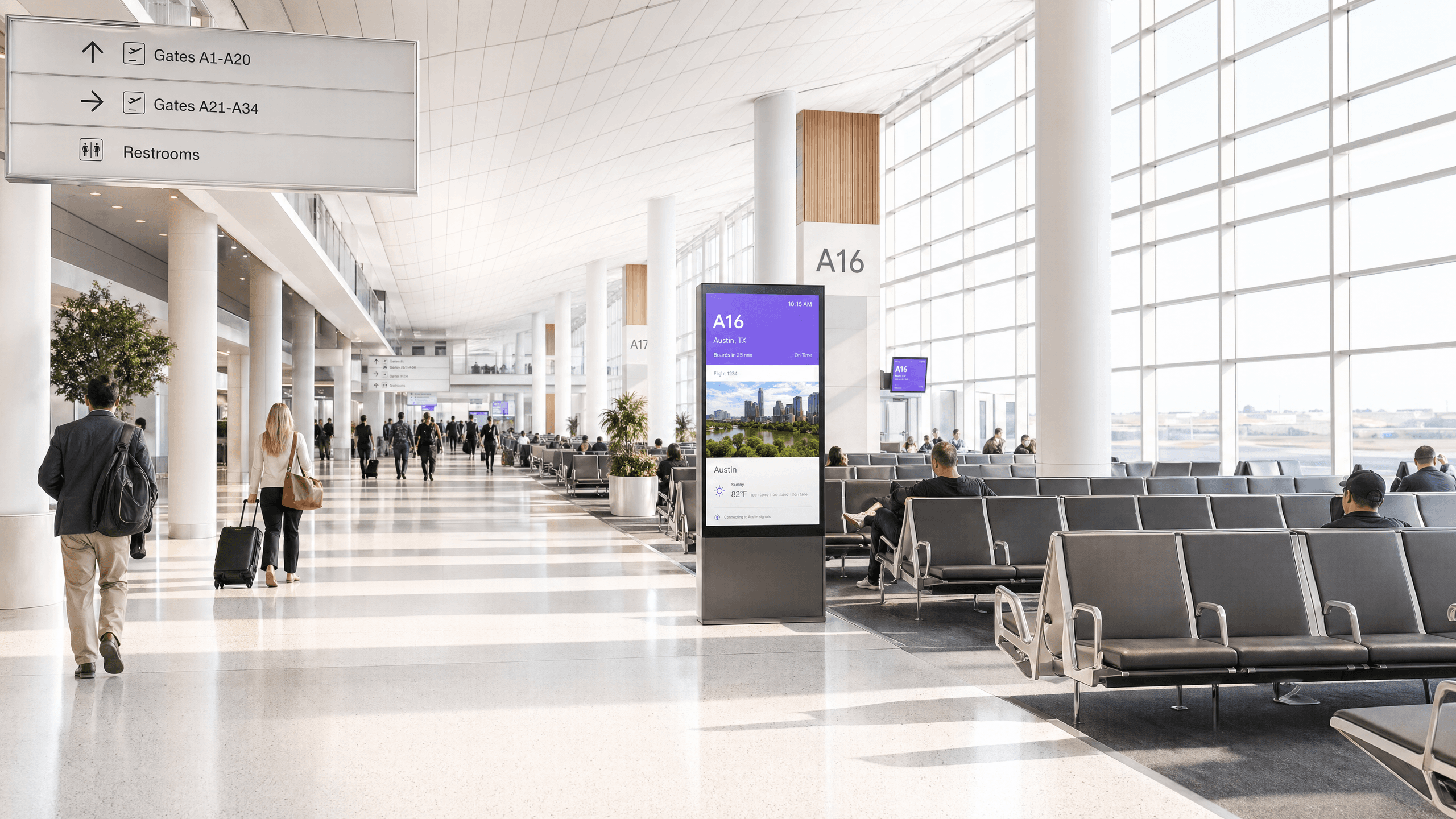
Airport WiFi: How Operators Deliver Connectivity Across Terminals
This guide provides IT leaders with actionable strategies for designing, deploying, and managing high-density airport WiFi networks. It covers technical architecture, RF planning, and how to utilise platforms like Purple to turn passenger connectivity into valuable analytics and revenue.
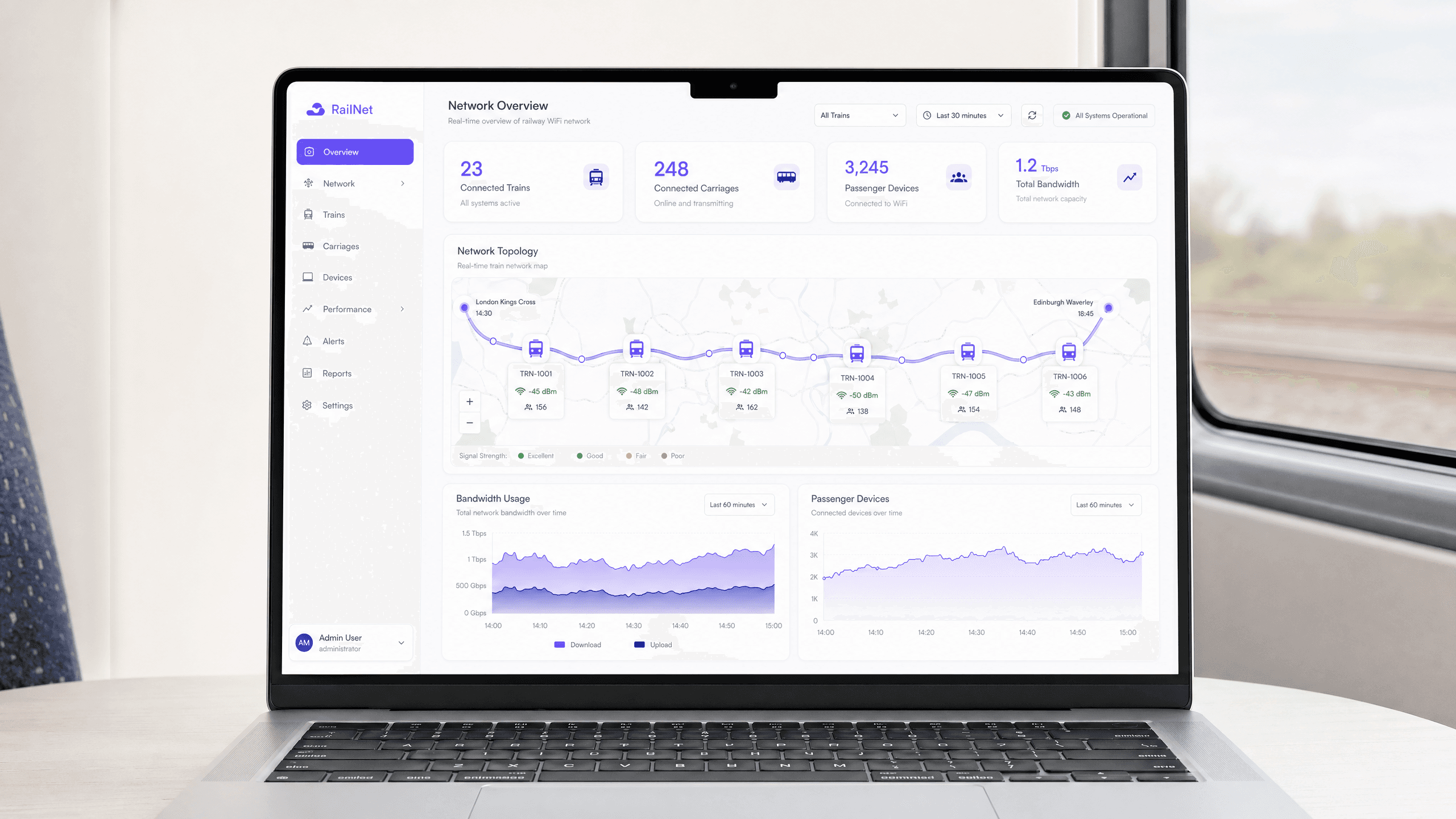
Railway WiFi Network: How Operators Are Delivering Connectivity at Speed
This technical reference guide provides actionable insights for IT leaders, network architects, and transport operations directors on architecting and deploying reliable railway WiFi networks. It covers the full stack from lineside infrastructure and multi-bearer aggregation to bandwidth management, captive portals, and passenger analytics. The guide demonstrates how operators can move beyond treating onboard WiFi as a cost centre and instead leverage it as a strategic asset that generates first-party data, operational intelligence, and measurable ROI.