Secure WiFi.
Easy to manage, easier to use.
Identity-based networks.
Certificate authentication.
No passwords. No captive portals.

WiFi authentication hasn’t evolved in 20 years
Live in over 80,000 venues
One platform. Three solutions.

Kill the captive
portal
Guests authenticate once with their email. Encrypted connection from the first packet using OpenRoaming. Automatic access on return visits. No captive portals, no shared passwords, no open networks.
- OpenRoaming and Passpoint certified
- Encrypted from the first packet
- Works across 80,000+ venues globally

Passwordless zero trust
Staff authenticate via their work IdP - no password to remember. Install once, connect everywhere across all devices. Automatic provisioning when they join, instant revocation when they leave. No certificates to manage.
- Works with Entra ID, Google, Okta
- Auto-revoke on directory change
- Cross-device profile sync

The at-home experience
Each tenant gets their own isolated network segment. See and connect all their devices. Staff authenticate via SSO, residents via email. Simple iPSK for legacy devices. Home WiFi simplicity, enterprise security.
- Works with Entra ID, Google, Okta
- Auto-revoke on directory change
- No on-prem RADIUS servers
Live in weeks, not months
Point your APs to Purple
Cloud overlay on Cisco, Aruba, Ruckus, Juniper Mist, Meraki, or Ubiquiti UniFi. No hardware swap.
Choose your sign-in flow
Branded captive portal for guests, 802.1X for staff against Entra ID / Okta / Google, iPSK per tenant for multi-tenant buildings.
Users connect securely
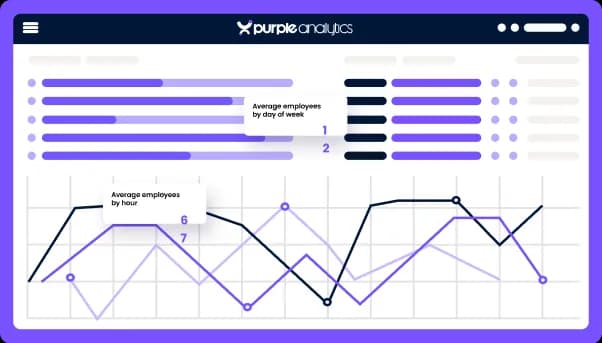
From the first session — with analytics, marketing automation, and per-device revocation from day one.
What our customers say
Purple's solution is integral to our overall business strategies - not only does it allow us to tailor the user's journey based on individual venues, but it also allows us to collect valuable, rich data that would otherwise have been unknown to the business. This allows us to drive visits with tailored communications, which ultimately leads to an ROI that pays for the software itself, and then some!

Compared to the other platforms we looked at, Purple is more robust, the reports are impressive and the portal is far more visually appealing and easy to understand. The automated emails are good for saving time, allowing us to focus on planning new marketing campaigns.

The feedback that we have received from patients about the WiFi has been very positive, the weekly KPIs that we receive from Purple’s portal prove that the offering is well used and the user demographics have proved particularly interesting. Our main demographic at the hospital is elderly patients and in initial discussions about WiFi many people believed that this age category wouldn’t use the service. However, this has not been the case as many of our older patients use it. This information is useful to justify the usage amongst our largest demographic
We’re excited to be utilising Purple to enrich our charity communications mix. It’ll allow us to raise awareness of charity initiatives and increase the reach of our mailing list whilst providing secure, accessible and free WiFi to patients and visitors.
This state-of-the-art system will not only improve the experience of patients visiting Croydon University Hospital by reducing the stresses that navigating a large site can cause, but will also help them plot the quickest route to their care or to the loved ones they are visiting.
It’s a delight to work with Purple. The focus on delivering value to your customers is very apparent and nothing is too much trouble. Engagement is quick and sessions are always rewarding, ensuring we can continue to grow, to help provide the best possible service to our passengers
I’ve never had a supplier who so thoroughly understands our needs and objectives. Purple showed a very intricate understanding of the ticket sales model and that the use of an on-board portal was critical in reaching that huge untapped base!
Purple has provided a platform that has helped us achieve our goal of elevating the fan experience.
With the implementation of Purple’s tools, we are now able to offer a high-quality service to our passengers while gathering insights that allow us to understand the needs and expectations of our different passenger profiles and thus be able to identify concrete actions to improve the customer experience.
We are continually looking for new ways to enhance the customer experience, and Purple has helped us do just that, with the added benefit of customer insight
Purple knows their tech but it’s their people and their dedication to their jobs and professionalism that stand out. They understand that digital wayfinding in a healthcare environment is more than just downloading a mobile app.
Purple has been a fantastic partner! They are always excited to support our business objectives and quick to respond to any emails/requests we may have enabling us to deliver against our organisational goals.
Purple has provided a gateway for us to begin building better customer profiles

IDENTITY PROVIDERS


NETWORK VENDORS




Ready to fix WiFi authentication?
See how identity-based networking works for your environment.