Technical Guides
Deep, expert-led guides covering guest WiFi, analytics, captive portals, and modern venue technology. Each guide includes diagrams, worked examples, and audio podcasts.

802.1X Authentication: Securing Network Access on Modern Devices
This guide provides a comprehensive, actionable overview of IEEE 802.1X authentication for senior IT professionals and network architects. It details the critical steps for securing network access across diverse enterprise environments, focusing on practical, vendor-neutral deployment guidance to mitigate risk, ensure compliance, and deliver a seamless, secure user experience.

802.1X Authentication: Securing Network Access on Modern Devices
This guide provides a comprehensive, actionable overview of IEEE 802.1X authentication for senior IT professionals and network architects. It details the critical steps for securing network access across diverse enterprise environments, focusing on practical, vendor-neutral deployment guidance to mitigate risk, ensure compliance, and deliver a seamless, secure user experience.

Securing Networks with Wi-Fi 7: A Technical Deep Dive
This guide provides a comprehensive technical reference on Wi-Fi 7 security features for enterprise IT teams, covering the mandatory enforcement of WPA3 encryption, the security implications of Multi-Link Operation (MLO), and the practical challenges of supporting legacy devices during migration. It equips network architects, IT managers, and CTOs at hotels, retail chains, stadiums, and public-sector organisations with actionable deployment strategies, compliance guidance aligned to PCI DSS and GDPR, and real-world case studies with measurable outcomes. Understanding these changes is critical for any organisation planning a wireless infrastructure upgrade this year, as Wi-Fi 7 represents a fundamental shift in the security baseline for enterprise wireless networks.

Securing Networks with Wi-Fi 7: A Technical Deep Dive
This guide provides a comprehensive technical reference on Wi-Fi 7 security features for enterprise IT teams, covering the mandatory enforcement of WPA3 encryption, the security implications of Multi-Link Operation (MLO), and the practical challenges of supporting legacy devices during migration. It equips network architects, IT managers, and CTOs at hotels, retail chains, stadiums, and public-sector organisations with actionable deployment strategies, compliance guidance aligned to PCI DSS and GDPR, and real-world case studies with measurable outcomes. Understanding these changes is critical for any organisation planning a wireless infrastructure upgrade this year, as Wi-Fi 7 represents a fundamental shift in the security baseline for enterprise wireless networks.
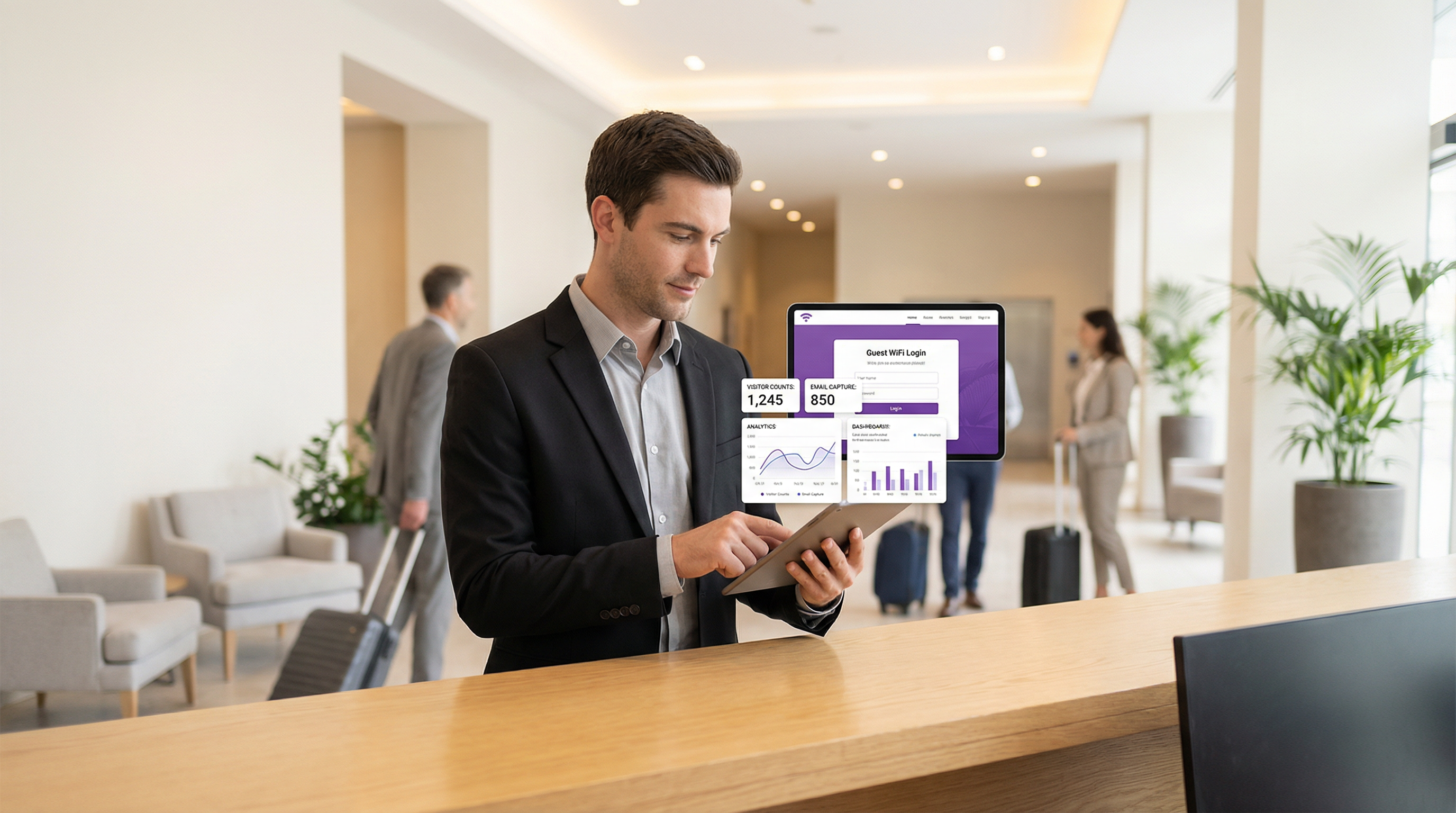
Guest WiFi Marketing: The Ultimate Guide to Capturing Leads, Driving Sales, and Enhancing Customer Experience
This guide provides a technical deep-dive into leveraging guest WiFi for marketing, lead capture, and customer analytics. It offers actionable strategies for IT managers and venue operators to transform their WiFi from a cost centre into a powerful, ROI-driven marketing platform, covering architecture, implementation, and compliance.
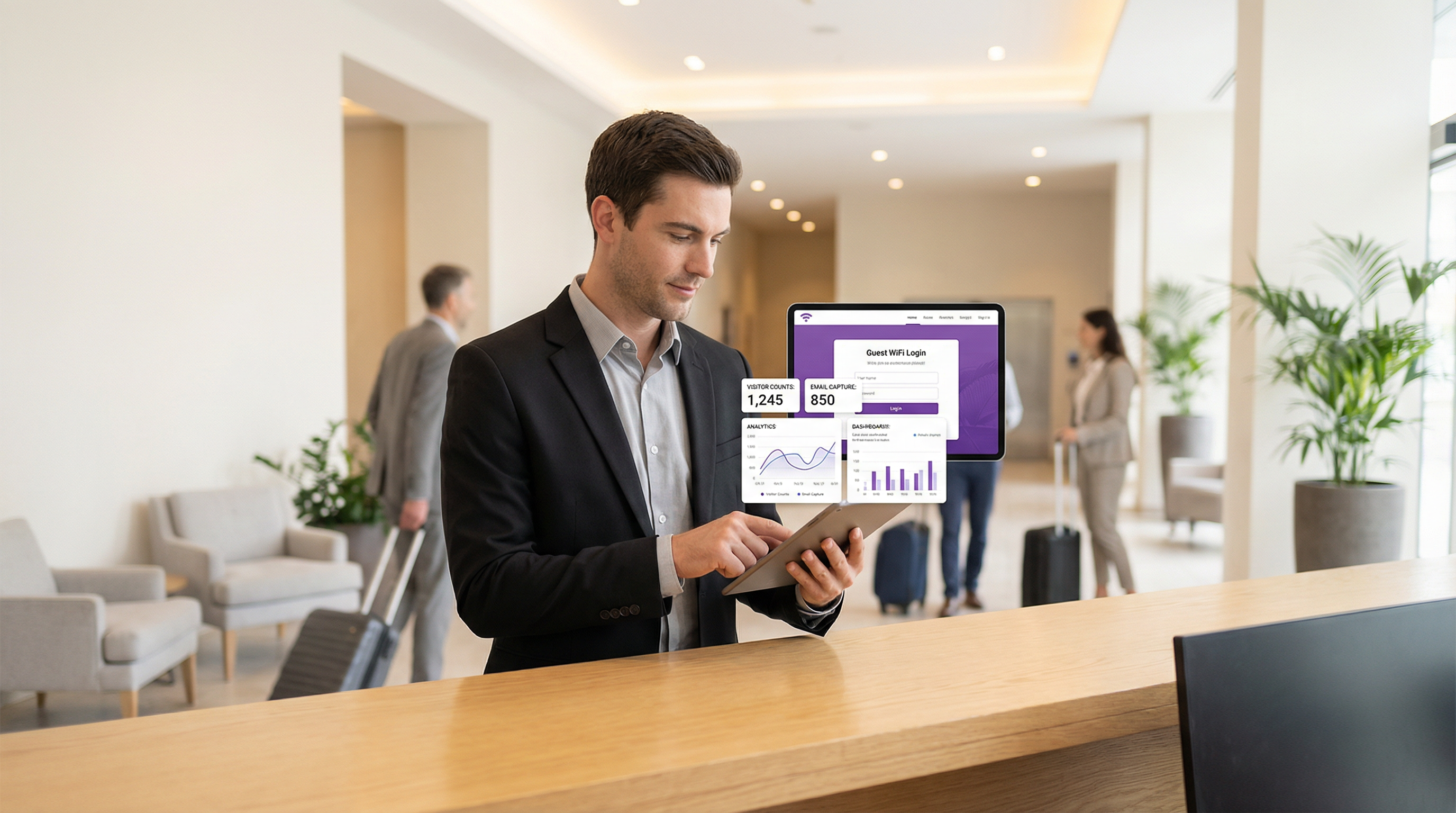
Guest WiFi Marketing: The Ultimate Guide to Capturing Leads, Driving Sales, and Enhancing Customer Experience
This guide provides a technical deep-dive into leveraging guest WiFi for marketing, lead capture, and customer analytics. It offers actionable strategies for IT managers and venue operators to transform their WiFi from a cost centre into a powerful, ROI-driven marketing platform, covering architecture, implementation, and compliance.

dotdigital (formerly Dotmailer): Integration Guide, Best Practices, and Troubleshooting for Purple AI Users
This guide provides Purple AI users — particularly IT managers, network architects, and CTOs at hotels, retail chains, stadiums, and conference centres — with a definitive technical reference for deploying and optimising the dotdigital (formerly Dotmailer) connector. It covers the end-to-end integration architecture, step-by-step configuration, GDPR-compliant data handling, automation programme design, and a structured troubleshooting framework. Organisations that implement this integration correctly convert guest WiFi logins into a high-value, consent-gated marketing database that drives measurable revenue outcomes.

dotdigital (formerly Dotmailer): Integration Guide, Best Practices, and Troubleshooting for Purple AI Users
This guide provides Purple AI users — particularly IT managers, network architects, and CTOs at hotels, retail chains, stadiums, and conference centres — with a definitive technical reference for deploying and optimising the dotdigital (formerly Dotmailer) connector. It covers the end-to-end integration architecture, step-by-step configuration, GDPR-compliant data handling, automation programme design, and a structured troubleshooting framework. Organisations that implement this integration correctly convert guest WiFi logins into a high-value, consent-gated marketing database that drives measurable revenue outcomes.

WiFi Hotspot 2.0 (Passpoint): The Ultimate Guide to Seamless and Secure WiFi Roaming
This guide provides a comprehensive technical overview of WiFi Hotspot 2.0 (Passpoint) for IT leaders. It details the technology, security benefits, and a step-by-step implementation framework for deploying seamless, secure WiFi roaming in enterprise environments like hotels, retail, and large venues, ultimately improving user experience and reducing operational overhead.

WiFi Hotspot 2.0 (Passpoint): The Ultimate Guide to Seamless and Secure WiFi Roaming
This guide provides a comprehensive technical overview of WiFi Hotspot 2.0 (Passpoint) for IT leaders. It details the technology, security benefits, and a step-by-step implementation framework for deploying seamless, secure WiFi roaming in enterprise environments like hotels, retail, and large venues, ultimately improving user experience and reducing operational overhead.

MDU Login: Simplifying WiFi Access in Multi-Dwelling Units
This technical reference guide provides IT managers, network architects, and CTOs with a definitive framework for deploying and managing WiFi access in Multi-Dwelling Units (MDUs), covering the trade-offs between shared PSK, WPA3-Enterprise 802.1X, and Identity PSK (iPSK) authentication models. It addresses the core operational challenges of RF interference, security segmentation, and resident lifecycle management, and demonstrates how a managed WiFi platform such as Purple transforms connectivity from a cost centre into a measurable revenue asset. Drawing on real-world deployment scenarios and referencing standards including IEEE 802.1X, WPA3, GDPR, and PCI DSS, the guide equips venue operators with the architecture, implementation steps, and ROI metrics needed to make an informed investment decision this quarter.

MDU Login: Simplifying WiFi Access in Multi-Dwelling Units
This technical reference guide provides IT managers, network architects, and CTOs with a definitive framework for deploying and managing WiFi access in Multi-Dwelling Units (MDUs), covering the trade-offs between shared PSK, WPA3-Enterprise 802.1X, and Identity PSK (iPSK) authentication models. It addresses the core operational challenges of RF interference, security segmentation, and resident lifecycle management, and demonstrates how a managed WiFi platform such as Purple transforms connectivity from a cost centre into a measurable revenue asset. Drawing on real-world deployment scenarios and referencing standards including IEEE 802.1X, WPA3, GDPR, and PCI DSS, the guide equips venue operators with the architecture, implementation steps, and ROI metrics needed to make an informed investment decision this quarter.

Metropolitan Area Networks (MANs): A Deep Dive into Technologies, Applications, and Future Trends
This guide provides a comprehensive technical reference on Metropolitan Area Networks (MANs) for IT leaders and network architects. It covers core technologies, deployment strategies, and business considerations for implementing high-performance, city-scale networks. The content is tailored for decision-makers in hospitality, retail, events, and public-sector organisations.

Metropolitan Area Networks (MANs): A Deep Dive into Technologies, Applications, and Future Trends
This guide provides a comprehensive technical reference on Metropolitan Area Networks (MANs) for IT leaders and network architects. It covers core technologies, deployment strategies, and business considerations for implementing high-performance, city-scale networks. The content is tailored for decision-makers in hospitality, retail, events, and public-sector organisations.

Understanding and Hardening RADIUS Against MD5 Collision Attacks
This guide provides a comprehensive technical reference on the RADIUS MD5 collision vulnerability (CVE-2024-3596, 'Blast-RADIUS'), explaining how man-in-the-middle attackers can exploit weaknesses in the MD5-based Response Authenticator to forge authentication approvals without knowing user credentials. It is essential reading for IT managers, network architects, and CTOs operating enterprise WiFi in hospitality, retail, events, and public-sector environments who need to assess their exposure, apply immediate mitigations, and plan a strategic migration to modern authentication standards. The guide covers the full attack lifecycle, a phased hardening roadmap, real-world deployment scenarios, and compliance implications under PCI DSS, GDPR, and ISO 27001.

Understanding and Hardening RADIUS Against MD5 Collision Attacks
This guide provides a comprehensive technical reference on the RADIUS MD5 collision vulnerability (CVE-2024-3596, 'Blast-RADIUS'), explaining how man-in-the-middle attackers can exploit weaknesses in the MD5-based Response Authenticator to forge authentication approvals without knowing user credentials. It is essential reading for IT managers, network architects, and CTOs operating enterprise WiFi in hospitality, retail, events, and public-sector environments who need to assess their exposure, apply immediate mitigations, and plan a strategic migration to modern authentication standards. The guide covers the full attack lifecycle, a phased hardening roadmap, real-world deployment scenarios, and compliance implications under PCI DSS, GDPR, and ISO 27001.
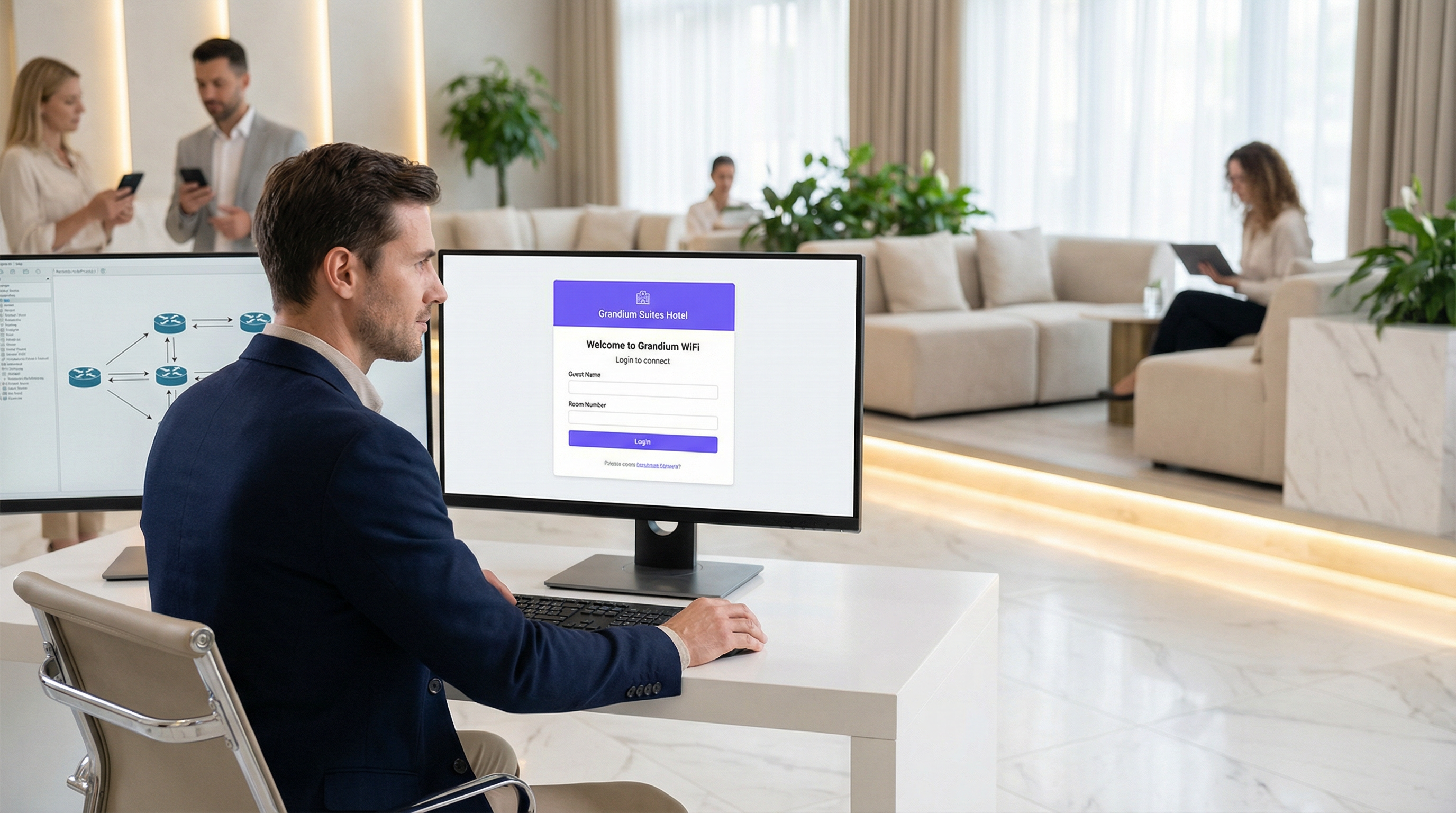
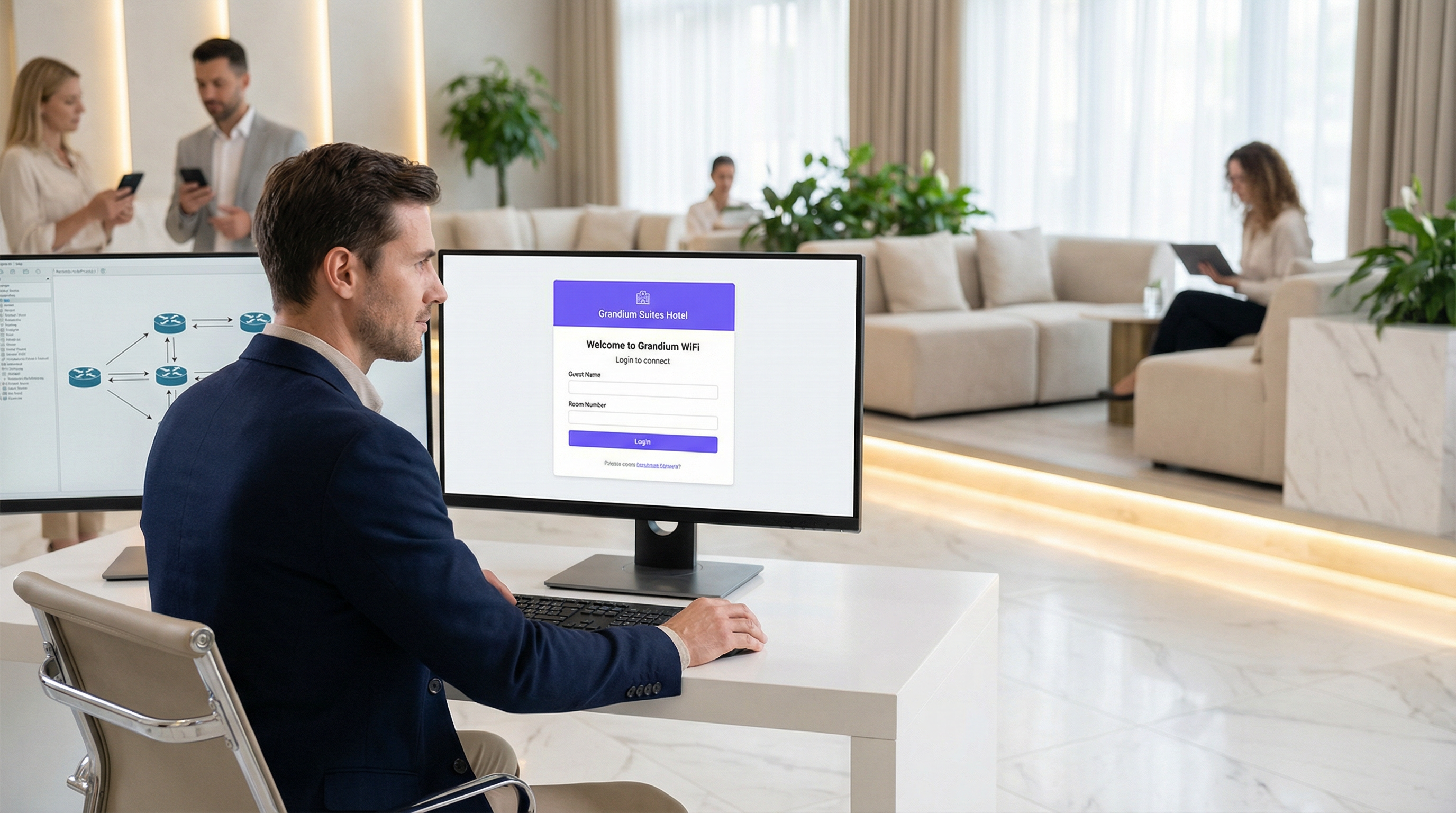
Captive Portals: A Comprehensive Guide to Implementation, Customization, and Security
This guide provides IT managers, network architects, and CTOs with a definitive technical reference for deploying, customising, and securing captive wifi portals across enterprise venues including hotels, retail chains, stadiums, and public-sector facilities. It covers authentication architectures, GDPR and PCI DSS compliance obligations, threat mitigation strategies, and the advanced analytics capabilities available through Purple's enterprise WiFi intelligence platform. Organisations that implement captive portals correctly transform a basic connectivity utility into a measurable business intelligence and revenue-generation asset.
Captive Portals: A Comprehensive Guide to Implementation, Customisation, and Security
This guide provides IT managers, network architects, and CTOs with a definitive technical reference for deploying, customising, and securing captive wifi portals across enterprise venues including hotels, retail chains, stadiums, and public-sector facilities. It covers authentication architectures, GDPR and PCI DSS compliance obligations, threat mitigation strategies, and the advanced analytics capabilities available through Purple's enterprise WiFi intelligence platform. Organisations that implement captive portals correctly transform a basic connectivity utility into a measurable business intelligence and revenue-generation asset.

The Definitive Timeline of WiFi: From ALOHAnet to WiFi 7 and Beyond
This guide provides a definitive technical timeline of WiFi, tracing its origins from the 1971 ALOHAnet experiment through every major IEEE 802.11 standard to the ratification of WiFi 7 in 2024 and the emerging WiFi 8 roadmap. It is designed for IT managers, network architects, and CTOs who need to understand the engineering evolution of wireless technology to make informed infrastructure investment decisions. By contextualising each generation's innovations within real-world deployment scenarios across hospitality, retail, and large venues, the guide delivers actionable guidance on upgrading, securing, and future-proofing enterprise wireless networks.

The Definitive Timeline of WiFi: From ALOHAnet to WiFi 7 and Beyond
This guide provides a definitive technical timeline of WiFi, tracing its origins from the 1971 ALOHAnet experiment through every major IEEE 802.11 standard to the ratification of WiFi 7 in 2024 and the emerging WiFi 8 roadmap. It is designed for IT managers, network architects, and CTOs who need to understand the engineering evolution of wireless technology to make informed infrastructure investment decisions. By contextualising each generation's innovations within real-world deployment scenarios across hospitality, retail, and large venues, the guide delivers actionable guidance on upgrading, securing, and future-proofing enterprise wireless networks.

Captive Portal Solutions: The Ultimate Guide for Businesses of All Sizes
This guide provides a comprehensive technical reference for IT managers, network architects, and CTOs on deploying effective captive portal solutions. It offers actionable guidance on architecture, vendor selection, and implementation to transform a network access point into a strategic asset for data collection, customer engagement, and ROI generation.

Captive Portal Solutions: The Ultimate Guide for Businesses of All Sizes
This guide provides a comprehensive technical reference for IT managers, network architects, and CTOs on deploying effective captive portal solutions. It offers actionable guidance on architecture, vendor selection, and implementation to transform a network access point into a strategic asset for data collection, customer engagement, and ROI generation.

Guest WiFi Captive Portals: The Ultimate Guide to Creating a Seamless and Secure User Experience
This guide provides IT leaders and venue operators with a comprehensive technical reference for designing, implementing, and securing guest WiFi captive portals at enterprise scale. It covers the full authentication architecture from RADIUS to CRM integration, GDPR compliance requirements, advanced customisation options including A/B testing and personalised content delivery for Purple AI users, and a proven ROI framework with real-world case studies from hospitality and retail environments.

Guest WiFi Captive Portals: The Ultimate Guide to Creating a Seamless and Secure User Experience
This guide provides IT leaders and venue operators with a comprehensive technical reference for designing, implementing, and securing guest WiFi captive portals at enterprise scale. It covers the full authentication architecture from RADIUS to CRM integration, GDPR compliance requirements, advanced customisation options including A/B testing and personalised content delivery for Purple AI users, and a proven ROI framework with real-world case studies from hospitality and retail environments.

Indoor Wayfinding: A Comprehensive Guide to Technologies, Applications, and Benefits for Businesses
This guide provides a comprehensive technical overview of indoor wayfinding for IT leaders and venue operators. It details the core technologies, deployment strategies, and business benefits, offering actionable guidance for implementing a system that enhances visitor experience and delivers measurable ROI.

Indoor Wayfinding: A Comprehensive Guide to Technologies, Applications, and Benefits for Businesses
This guide provides a comprehensive technical overview of indoor wayfinding for IT leaders and venue operators. It details the core technologies, deployment strategies, and business benefits, offering actionable guidance for implementing a system that enhances visitor experience and delivers measurable ROI.
Build Your Own Captive Portal App: A Developer's Guide (with Code Examples)
This technical guide provides developers and IT leaders with a comprehensive framework for building custom captive portal applications. It covers architectural design, platform selection (iOS, Android, Web), security best practices (802.1X, GDPR), and API integration strategies to transform guest WiFi into a powerful tool for customer engagement and data analytics.
Build Your Own Captive Portal App: A Developer's Guide (with Code Examples)
This technical guide provides developers and IT leaders with a comprehensive framework for building custom captive portal applications. It covers architectural design, platform selection (iOS, Android, Web), security best practices (802.1X, GDPR), and API integration strategies to transform guest WiFi into a powerful tool for customer engagement and data analytics.
Staff WiFi: A Comprehensive Guide to Secure and Efficient Network Access for Employees
A comprehensive technical reference for IT leaders on designing, deploying, and managing secure, high-performance staff WiFi networks. This guide provides actionable best practices for authentication, network segmentation, and bandwidth management to enhance operational efficiency and mitigate security risks.
Staff WiFi: A Comprehensive Guide to Secure and Efficient Network Access for Employees
A comprehensive technical reference for IT leaders on designing, deploying, and managing secure, high-performance staff WiFi networks. This guide provides actionable best practices for authentication, network segmentation, and bandwidth management to enhance operational efficiency and mitigate security risks.

Personal Area Networks (PANs): A Comprehensive Guide to Technologies, Security, and Applications
This guide provides a comprehensive technical reference on Personal Area Networks (PANs) for IT leaders and network architects. It covers the core technologies, critical security considerations for enterprise deployments, and practical implementation guidance for leveraging PANs in venues like hotels, retail, and stadiums to enhance operational efficiency and customer experience.

Personal Area Networks (PANs): A Comprehensive Guide to Technologies, Security, and Applications
This guide provides a comprehensive technical reference on Personal Area Networks (PANs) for IT leaders and network architects. It covers the core technologies, critical security considerations for enterprise deployments, and practical implementation guidance for leveraging PANs in venues like hotels, retail, and stadiums to enhance operational efficiency and customer experience.

Captive Portal Login Apps: Choosing the Right Solution for Your Business (Features, Security, and Pricing)
This guide provides a comprehensive technical reference for IT leaders evaluating, deploying, and managing captive portal login solutions across enterprise venues. It covers critical features, security protocols, authentication methods, pricing models, and integration capabilities to help businesses enhance network security, ensure regulatory compliance, and maximise the ROI of their guest WiFi infrastructure.

Captive Portal Login Apps: Choosing the Right Solution for Your Business (Features, Security, and Pricing)
This guide provides a comprehensive technical reference for IT leaders evaluating, deploying, and managing captive portal login solutions across enterprise venues. It covers critical features, security protocols, authentication methods, pricing models, and integration capabilities to help businesses enhance network security, ensure regulatory compliance, and maximise the ROI of their guest WiFi infrastructure.

Captive Portal Login: Troubleshooting Common Issues and Optimizing User Experience
This authoritative technical reference guide equips IT managers, network architects, and CTOs with a comprehensive framework for diagnosing and resolving captive portal login failures, selecting the optimal authentication strategy for their venue type, and measuring portal performance against business KPIs. Drawing on real-world deployment scenarios across hospitality, retail, and public-sector environments, it covers the full lifecycle from architecture and compliance to step-by-step troubleshooting for platforms including Purple AI, UniFi, Meraki, and MikroTik. For any organisation operating guest or public WiFi, a poorly performing captive portal is a direct revenue and reputation risk — this guide provides the decision frameworks and operational playbooks to eliminate that risk.

Captive Portal Login: Troubleshooting Common Issues and Optimising User Experience
This authoritative technical reference guide equips IT managers, network architects, and CTOs with a comprehensive framework for diagnosing and resolving captive portal login failures, selecting the optimal authentication strategy for their venue type, and measuring portal performance against business KPIs. Drawing on real-world deployment scenarios across hospitality, retail, and public-sector environments, it covers the full lifecycle from architecture and compliance to step-by-step troubleshooting for platforms including Purple AI, UniFi, Meraki, and MikroTik. For any organisation operating guest or public WiFi, a poorly performing captive portal is a direct revenue and reputation risk — this guide provides the decision frameworks and operational playbooks to eliminate that risk.

MAC Address Randomisation: A Deep Dive into Privacy Enhancement and its Impact on Network Management
This guide provides a comprehensive technical overview of MAC address randomization, a critical privacy feature now default on iOS, Android, and Windows devices. It details the direct impact on enterprise WiFi network management — from broken MAC-based authentication and inflated analytics to security monitoring gaps — and offers actionable, identity-driven strategies for IT leaders in hospitality, retail, stadiums, and public-sector organisations to adapt their infrastructure. By shifting from hardware-based to credential-based network management, organisations can simultaneously enhance security, achieve privacy compliance, and unlock richer customer insights.

MAC Address Randomization: A Deep Dive into Privacy Enhancement and its Impact on Network Management
This guide provides a comprehensive technical overview of MAC address randomization, a critical privacy feature now default on iOS, Android, and Windows devices. It details the direct impact on enterprise WiFi network management — from broken MAC-based authentication and inflated analytics to security monitoring gaps — and offers actionable, identity-driven strategies for IT leaders in hospitality, retail, stadiums, and public-sector organisations to adapt their infrastructure. By shifting from hardware-based to credential-based network management, organisations can simultaneously enhance security, achieve privacy compliance, and unlock richer customer insights.

Passpoint (Hotspot 2.0): A Comprehensive Guide to Secure and Seamless WiFi Roaming
This guide provides a comprehensive technical overview of Passpoint (Hotspot 2.0) for IT leaders and network architects, covering the IEEE 802.11u standard, GAS/ANQP discovery protocols, WPA3-Enterprise security, and the WBA OpenRoaming federation. It delivers a vendor-neutral implementation framework with phased deployment guidance, real-world case studies from hospitality and retail, and a clear analysis of the ROI and compliance benefits for enterprise venue operators.

Passpoint (Hotspot 2.0): A Comprehensive Guide to Secure and Seamless WiFi Roaming
This guide provides a comprehensive technical overview of Passpoint (Hotspot 2.0) for IT leaders and network architects, covering the IEEE 802.11u standard, GAS/ANQP discovery protocols, WPA3-Enterprise security, and the WBA OpenRoaming federation. It delivers a vendor-neutral implementation framework with phased deployment guidance, real-world case studies from hospitality and retail, and a clear analysis of the ROI and compliance benefits for enterprise venue operators.

WiFi Data Capture: A Comprehensive Guide to Privacy, Compliance, and Best Practices
This guide provides IT leaders with a comprehensive technical reference for implementing WiFi data capture solutions. It focuses on navigating the complex landscape of privacy, legal compliance (GDPR, CCPA), and data ethics, offering actionable best practices for venue operators in hospitality, retail, and large public spaces.

WiFi Data Capture: A Comprehensive Guide to Privacy, Compliance, and Best Practices
This guide provides IT leaders with a comprehensive technical reference for implementing WiFi data capture solutions. It focuses on navigating the complex landscape of privacy, legal compliance (GDPR, CCPA), and data ethics, offering actionable best practices for venue operators in hospitality, retail, and large public spaces.

WPA3-Enterprise: A Comprehensive Deployment Guide
This guide provides enterprise IT teams, network architects, and CTOs with a definitive, vendor-neutral reference for deploying WPA3-Enterprise across hospitality, retail, events, and public-sector environments. It covers the full deployment lifecycle — from hardware and RADIUS infrastructure requirements through phased migration strategy and client device configuration — while addressing the specific security improvements WPA3-Enterprise delivers over WPA2-Enterprise, including mandatory Protected Management Frames, enforced server certificate validation, and forward secrecy. Teams will find actionable configuration guidance, real-world case studies, and a structured troubleshooting framework to de-risk their migration and demonstrate compliance with PCI DSS v4.0 and GDPR Article 32.

WPA3-Enterprise: A Comprehensive Deployment Guide
This guide provides enterprise IT teams, network architects, and CTOs with a definitive, vendor-neutral reference for deploying WPA3-Enterprise across hospitality, retail, events, and public-sector environments. It covers the full deployment lifecycle — from hardware and RADIUS infrastructure requirements through phased migration strategy and client device configuration — while addressing the specific security improvements WPA3-Enterprise delivers over WPA2-Enterprise, including mandatory Protected Management Frames, enforced server certificate validation, and forward secrecy. Teams will find actionable configuration guidance, real-world case studies, and a structured troubleshooting framework to de-risk their migration and demonstrate compliance with PCI DSS v4.0 and GDPR Article 32.

Guest WiFi: The Ultimate Guide for Businesses to Enhance Customer Experience and Gather Valuable Data
This guide is the definitive technical reference for IT leaders and venue operators on deploying enterprise-grade guest WiFi. It provides actionable guidance on network architecture, security, and data analytics to transform guest WiFi from a cost centre into a powerful tool for enhancing customer experience and driving business intelligence.

Guest WiFi: The Ultimate Guide for Businesses to Enhance Customer Experience and Gather Valuable Data
This guide is the definitive technical reference for IT leaders and venue operators on deploying enterprise-grade guest WiFi. It provides actionable guidance on network architecture, security, and data analytics to transform guest WiFi from a cost centre into a powerful tool for enhancing customer experience and driving business intelligence.

Campus Area Networks (CANs): A Comprehensive Guide to Design, Implementation, and Management
This comprehensive technical reference guide covers the full lifecycle of Campus Area Networks (CANs) — from architectural design and technology selection to implementation, security hardening, and ongoing management. It is written for IT managers, network architects, and CTOs at hotels, retail chains, stadiums, and corporate campuses who need to build or modernise a high-performance, resilient connectivity backbone. By combining vendor-neutral best practices, real-world case studies, and actionable frameworks, this guide equips senior technical professionals to make informed decisions that deliver measurable ROI and support long-term strategic objectives.

Campus Area Networks (CANs): A Comprehensive Guide to Design, Implementation, and Management
This comprehensive technical reference guide covers the full lifecycle of Campus Area Networks (CANs) — from architectural design and technology selection to implementation, security hardening, and ongoing management. It is written for IT managers, network architects, and CTOs at hotels, retail chains, stadiums, and corporate campuses who need to build or modernise a high-performance, resilient connectivity backbone. By combining vendor-neutral best practices, real-world case studies, and actionable frameworks, this guide equips senior technical professionals to make informed decisions that deliver measurable ROI and support long-term strategic objectives.
WiFi Captive Portals: The Ultimate Guide to Setup, Security, and Customisation
This authoritative technical reference guide covers the full lifecycle of enterprise WiFi captive portal deployment, from network architecture and security hardening to GDPR and CCPA compliance and measurable business ROI. It is designed for IT managers, network architects, and CTOs at hotels, retail chains, stadiums, and public-sector organisations who need actionable, vendor-neutral guidance to implement, secure, and optimise guest WiFi infrastructure. The guide includes step-by-step configuration instructions, real-world case studies, security checklists, compliance frameworks, and a discussion of how captive portals drive first-party data acquisition and customer analytics at scale.
WiFi Captive Portals: The Ultimate Guide to Setup, Security, and Customization
This authoritative technical reference guide covers the full lifecycle of enterprise WiFi captive portal deployment, from network architecture and security hardening to GDPR and CCPA compliance and measurable business ROI. It is designed for IT managers, network architects, and CTOs at hotels, retail chains, stadiums, and public-sector organisations who need actionable, vendor-neutral guidance to implement, secure, and optimise guest WiFi infrastructure. The guide includes step-by-step configuration instructions, real-world case studies, security checklists, compliance frameworks, and a discussion of how captive portals drive first-party data acquisition and customer analytics at scale.



